mirror of
https://github.com/sadoyan/aralez.git
synced 2026-04-30 23:08:40 +08:00
Compare commits
8 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
ece4fa20af | ||
|
|
2ad3a059ab | ||
|
|
6f012cee69 | ||
|
|
51c88c8f7c | ||
|
|
f91bc41103 | ||
|
|
21e1276ff5 | ||
|
|
8463cdabbc | ||
|
|
d0e4b52ce6 |
1
.gitignore
vendored
1
.gitignore
vendored
@@ -8,6 +8,7 @@
|
||||
/target/
|
||||
*.iml
|
||||
.idea/
|
||||
.etc/
|
||||
*.ipr
|
||||
*.iws
|
||||
/out/
|
||||
|
||||
11
Cargo.lock
generated
11
Cargo.lock
generated
@@ -128,9 +128,11 @@ dependencies = [
|
||||
"log",
|
||||
"mimalloc",
|
||||
"notify",
|
||||
"once_cell",
|
||||
"pingora",
|
||||
"pingora-core",
|
||||
"pingora-http",
|
||||
"pingora-limits",
|
||||
"pingora-proxy",
|
||||
"prometheus 0.14.0",
|
||||
"rand 0.9.1",
|
||||
@@ -2085,6 +2087,15 @@ dependencies = [
|
||||
"crc32fast",
|
||||
]
|
||||
|
||||
[[package]]
|
||||
name = "pingora-limits"
|
||||
version = "0.5.0"
|
||||
source = "registry+https://github.com/rust-lang/crates.io-index"
|
||||
checksum = "a719a8cb5558ca06bd6076c97b8905d500ea556da89e132ba53d4272844f95b9"
|
||||
dependencies = [
|
||||
"ahash",
|
||||
]
|
||||
|
||||
[[package]]
|
||||
name = "pingora-load-balancing"
|
||||
version = "0.5.0"
|
||||
|
||||
@@ -19,6 +19,7 @@ dashmap = "7.0.0-rc2"
|
||||
pingora-core = "0.5.0"
|
||||
pingora-proxy = "0.5.0"
|
||||
pingora-http = "0.5.0"
|
||||
pingora-limits = "0.5.0"
|
||||
#pingora-pool = "0.5.0"
|
||||
async-trait = "0.1.88"
|
||||
env_logger = "0.11.8"
|
||||
@@ -48,5 +49,7 @@ lazy_static = "1.5.0"
|
||||
x509-parser = "0.17.0"
|
||||
rustls-pemfile = "2.2.0"
|
||||
tower-http = { version = "0.6.6", features = ["fs"] }
|
||||
once_cell = "1.20.2"
|
||||
#moka = { version = "0.12.10", features = ["sync"] }
|
||||
|
||||
|
||||
|
||||
52
README.md
52
README.md
@@ -15,6 +15,9 @@ Built on Rust, on top of **Cloudflare’s Pingora engine**, **Aralez** delivers
|
||||
- **TLS Termination** — Built-in OpenSSL support.
|
||||
- **Automatic load of certificates** — Automatically reads and loads certificates from a folder, without a restart.
|
||||
- **Upstreams TLS detection** — Aralez will automatically detect if upstreams uses secure connection.
|
||||
- **Built in rate limiter** — Limit requests to server, by setting up upper limit for requests per seconds, per virtualhost.
|
||||
- **Global rate limiter** — Set rate limit for all virtualhosts.
|
||||
- **Per path rate limiter** — Set rate limit for specific paths. Path limits will override global limits.
|
||||
- **Authentication** — Supports Basic Auth, API tokens, and JWT verification.
|
||||
- **Basic Auth**
|
||||
- **API Key** via `x-api-key` header
|
||||
@@ -87,6 +90,7 @@ Built on Rust, on top of **Cloudflare’s Pingora engine**, **Aralez** delivers
|
||||
| **master_key** | 5aeff7f9-7b94-447c-af60-e8c488544a3e | Master key for working with API server and JWT Secret generation |
|
||||
| **file_server_folder** | /some/local/folder | Optional, local folder to serve |
|
||||
| **file_server_address** | 127.0.0.1:3002 | Optional, Local address for file server. Can set as upstream for public access |
|
||||
| **config_api_enabled** | true | Boolean to enable/disable remote config push capability |
|
||||
|
||||
### 🌐 `upstreams.yaml`
|
||||
|
||||
@@ -114,6 +118,24 @@ File names:
|
||||
| `aralez-aarch64-musl.gz` | Static Linux ARM64 binary, without any system dependency |
|
||||
| `aralez-aarch64-glibc.gz` | Dynamic Linux ARM64 binary, with minimal system dependencies |
|
||||
|
||||
## 💡 Note
|
||||
|
||||
In general **glibc** builds are working faster, but have few, basic, system dependencies for example :
|
||||
|
||||
```
|
||||
linux-vdso.so.1 (0x00007ffeea33b000)
|
||||
libgcc_s.so.1 => /lib/x86_64-linux-gnu/libgcc_s.so.1 (0x00007f09e7377000)
|
||||
libm.so.6 => /lib/x86_64-linux-gnu/libm.so.6 (0x00007f09e6320000)
|
||||
libc.so.6 => /lib/x86_64-linux-gnu/libc.so.6 (0x00007f09e613f000)
|
||||
/lib64/ld-linux-x86-64.so.2 (0x00007f09e73b1000)
|
||||
```
|
||||
|
||||
These are common to any Linux systems, so the binary should work on almost any Linux system.
|
||||
|
||||
**musl** builds are 100% portable, static compiled binaries and have zero system depencecies.
|
||||
In general musl builds have a little less performance.
|
||||
The most intensive tests shows 107k-110k requests per second on **Glibc** binaries against 97k-100k **Musl** ones.
|
||||
|
||||
## 🔌 Running the Proxy
|
||||
|
||||
```bash
|
||||
@@ -146,6 +168,7 @@ A sample `upstreams.yaml` entry:
|
||||
provider: "file"
|
||||
sticky_sessions: false
|
||||
to_https: false
|
||||
rate_limit: 10
|
||||
headers:
|
||||
- "Access-Control-Allow-Origin:*"
|
||||
- "Access-Control-Allow-Methods:POST, GET, OPTIONS"
|
||||
@@ -156,6 +179,7 @@ authorization:
|
||||
myhost.mydomain.com:
|
||||
paths:
|
||||
"/":
|
||||
rate_limit: 20
|
||||
to_https: false
|
||||
headers:
|
||||
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
||||
@@ -176,13 +200,18 @@ myhost.mydomain.com:
|
||||
|
||||
- Sticky sessions are disabled globally. This setting applies to all upstreams. If enabled all requests will be 301 redirected to HTTPS.
|
||||
- HTTP to HTTPS redirect disabled globally, but can be overridden by `to_https` setting per upstream.
|
||||
- Requests to each hosted domains will be limited to 10 requests per second per virtualhost.
|
||||
- Requests limits are calculated per requester ip plus requested virtualhost.
|
||||
- If the requester exceeds the limit it will receive `429 Too Many Requests` error.
|
||||
- Optional. Rate limiter will be disabled if the parameter is entirely removed from config.
|
||||
- Requests to `myhost.mydomain.com/` will be limited to 20 requests per second.
|
||||
- Requests to `myhost.mydomain.com/` will be proxied to `127.0.0.1` and `127.0.0.2`.
|
||||
- Plain HTTP to `myhost.mydomain.com/foo` will get 301 redirect to configured TLS port of Aralez.
|
||||
- Requests to `myhost.mydomain.com/foo` will be proxied to `127.0.0.4` and `127.0.0.5`.
|
||||
- SSL/TLS for upstreams is detected automatically, no need to set any config parameter.
|
||||
- Assuming the `127.0.0.5:8443` is SSL protected. The inner traffic will use TLS.
|
||||
- Self signed certificates are silently accepted.
|
||||
- Global headers (CORS for this case) will be injected to all upstreams
|
||||
- Self-signed certificates are silently accepted.
|
||||
- Global headers (CORS for this case) will be injected to all upstreams.
|
||||
- Additional headers will be injected into the request for `myhost.mydomain.com`.
|
||||
- You can choose any path, deep nested paths are supported, the best match chosen.
|
||||
- All requests to servers will require JWT token authentication (You can comment out the authorization to disable it),
|
||||
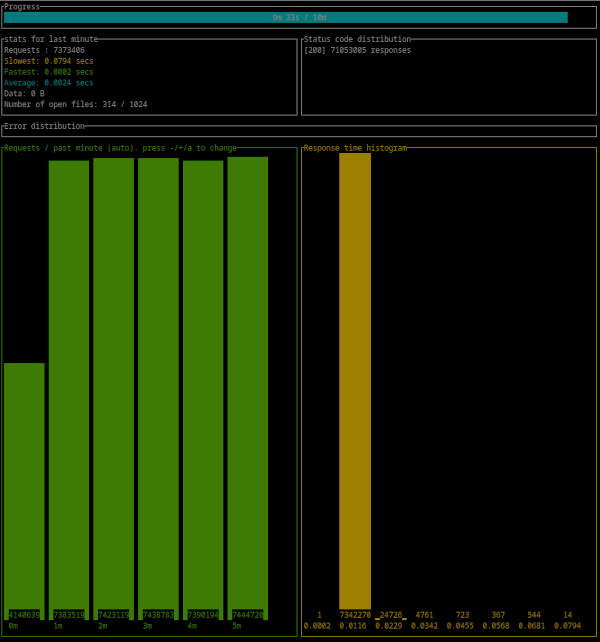
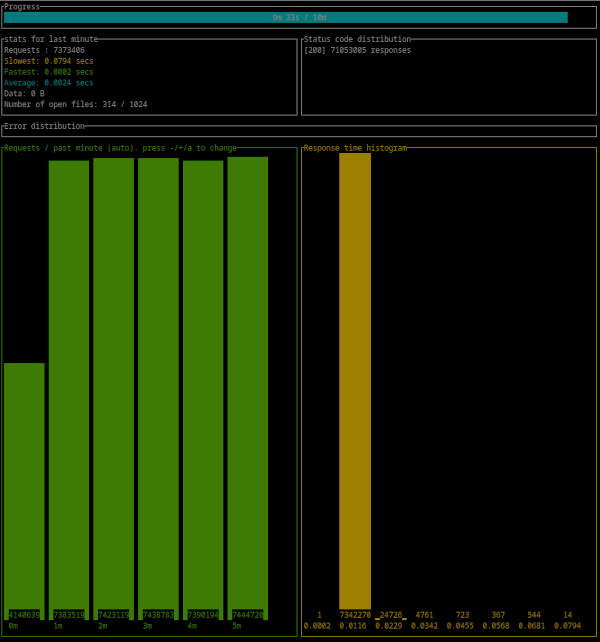
@@ -446,4 +475,21 @@ Error distribution:
|
||||
[228] aborted due to deadline
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
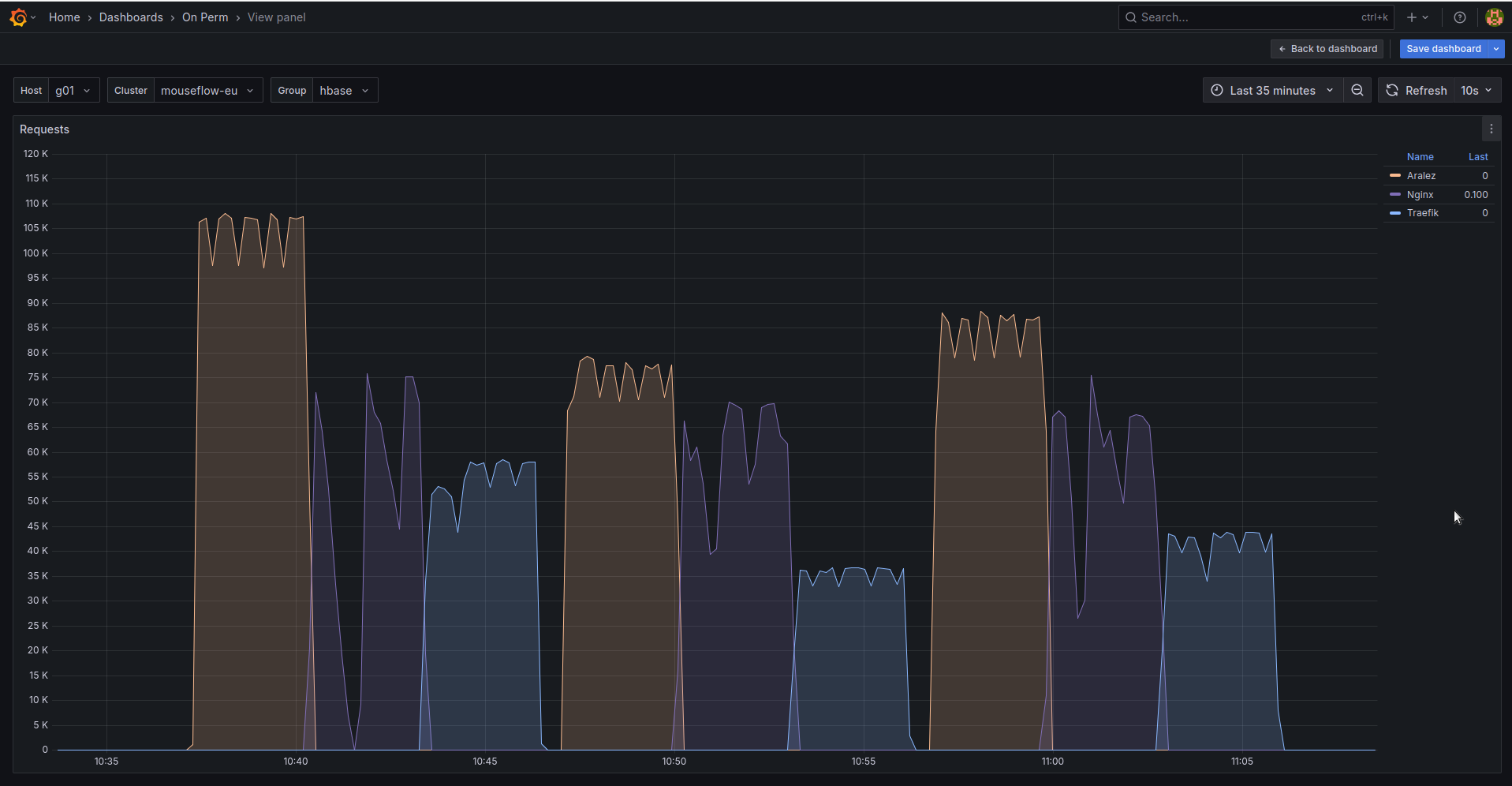
## 🚀 Aralez, Nginx, Traefik performance benchmark
|
||||
|
||||
This benchmark is done on 4 servers. With CPU Intel(R) Xeon(R) E-2174G CPU @ 3.80GHz, 64 GB RAM.
|
||||
|
||||
1. Sever runs Aralez, Traefik, Nginx on different ports. Tuned as much as I could .
|
||||
2. 3x Upstreams servers, running Nginx. Replying with dummy json hardcoded in config file for max performance.
|
||||
|
||||
All servers are connected to the same switch with 1GB port in datacenter , not a home lab. The results:
|
||||
|
||||
|
||||
The results show requests per second performed by Load balancer. You can see 3 batches with 800 concurrent users.
|
||||
|
||||
1. Requests via http1.1 to plain text endpoint.
|
||||
2. Requests to via http2 to SSL endpoint.
|
||||
3. Mixed workload with plain http1.1 and htt2 SSL.
|
||||
|
||||
|
||||
BIN
assets/bench.png
Normal file
BIN
assets/bench.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 160 KiB |
@@ -1,22 +1,23 @@
|
||||
# Main configuration file , applied on startup
|
||||
threads: 12 # Nubber of daemon threads default setting
|
||||
#user: aralez # Username for running aralez after dropping root privileges, requires program to start as root
|
||||
#group: aralez # Group for running aralez after dropping root privileges, requires program to start as root
|
||||
# Main configuration file, applied on startup
|
||||
threads: 12 # Number of daemon threads default setting
|
||||
#user: pastor # Username for running aralez after dropping root privileges, requires program to start as root
|
||||
#group: pastor # Group for running aralez after dropping root privileges, requires program to start as root
|
||||
daemon: false # Run in background
|
||||
upstream_keepalive_pool_size: 500 # Pool size for upstream keepalive connections
|
||||
pid_file: /tmp/aralez.pid # Path to PID file
|
||||
error_log: /tmp/aralez_err.log # Path to error log
|
||||
upgrade_sock: /tmp/aralez.sock # Path to socket file
|
||||
config_api_enabled: true # Boolean to enable/disable remote config push capability.
|
||||
config_address: 0.0.0.0:3000 # HTTP API address for pushing upstreams.yaml from remote location
|
||||
config_tls_address: 0.0.0.0:3001 # HTTP TLS API address for pushing upstreams.yaml from remote location
|
||||
config_tls_certificate: etc/server.crt # Mandatory if config_tls_address is set
|
||||
config_tls_key_file: etc/key.pem # Mandatory if config_tls_address is set
|
||||
config_tls_certificate: /opt/Rust/Projects/asyncweb/etc/server.crt # Mandatory if config_tls_address is set
|
||||
config_tls_key_file: /opt/Rust/Projects/asyncweb/etc/key.pem # Mandatory if config_tls_address is set
|
||||
proxy_address_http: 0.0.0.0:6193 # Proxy HTTP bind address
|
||||
proxy_address_tls: 0.0.0.0:6194 # Optional, Proxy TLS bind address
|
||||
proxy_certificates: etc/certificates # Mandatory if proxy_address_tls set, should contain certificate and key files strictly in a format {NAME}.crt, {NAME}.key.
|
||||
upstreams_conf: etc/upstreams.yaml # the location of upstreams file
|
||||
#file_server_folder: /some/path # Optional, local folder to serve
|
||||
#file_server_address: 127.0.0.1:3002 # Optional, Local address for file server. Can set as upstream for public access.
|
||||
proxy_certificates: /opt/Rust/Projects/asyncweb/etc/yoyo # Mandatory if proxy_address_tls set, should contain certificate and key files strictly in a format {NAME}.crt, {NAME}.key.
|
||||
upstreams_conf: /opt/Rust/Projects/asyncweb/etc/upstreams.yaml # the location of upstreams file
|
||||
file_server_folder: /opt/storage # Optional, local folder to serve
|
||||
file_server_address: 127.0.0.1:3002 # Optional, Local address for file server. Can set as upstream for public access.
|
||||
log_level: info # info, warn, error, debug, trace, off
|
||||
hc_method: HEAD # Healthcheck method (HEAD, GET, POST are supported) UPPERCASE
|
||||
hc_interval: 2 #Interval for health checks in seconds
|
||||
|
||||
@@ -2,6 +2,7 @@
|
||||
provider: "file" # consul
|
||||
sticky_sessions: false
|
||||
to_ssl: false
|
||||
#rate_limit: 100
|
||||
headers:
|
||||
- "Access-Control-Allow-Origin:*"
|
||||
- "Access-Control-Allow-Methods:POST, GET, OPTIONS"
|
||||
@@ -16,9 +17,9 @@ authorization:
|
||||
# creds: "5ecbf799-1343-4e94-a9b5-e278af5cd313-56b45249-1839-4008-a450-a60dc76d2bae"
|
||||
consul: # If the provider is consul. Otherwise, ignored.
|
||||
servers:
|
||||
- "http://master1:8500"
|
||||
- "http://192.168.22.1:8500"
|
||||
- "http://master1.foo.local:8500"
|
||||
- "http://consul1:8500"
|
||||
- "http://consul2:8500"
|
||||
- "http://consul3:8500"
|
||||
services: # proxy: The hostname to access the proxy server, real : The real service name in Consul database.
|
||||
- proxy: "proxy-frontend-dev-frontend-srv"
|
||||
real: "frontend-dev-frontend-srv"
|
||||
@@ -26,10 +27,11 @@ consul: # If the provider is consul. Otherwise, ignored.
|
||||
upstreams:
|
||||
myip.mydomain.com:
|
||||
paths:
|
||||
rate_limit: 10 # Per path rate limit have higher priority than global rate limit. If not set, the global rate limit will be used
|
||||
"/":
|
||||
to_https: false
|
||||
headers:
|
||||
- "X-Proxy-From:Gazan"
|
||||
- "X-Proxy-From:Aralez"
|
||||
servers: # List of upstreams HOST:PORT
|
||||
- "127.0.0.1:8000"
|
||||
- "127.0.0.2:8000"
|
||||
@@ -39,7 +41,7 @@ upstreams:
|
||||
to_https: true
|
||||
headers:
|
||||
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
||||
- "X-Proxy-From:Gazan"
|
||||
- "X-Proxy-From:Aralez"
|
||||
servers:
|
||||
- "127.0.0.1:8000"
|
||||
- "127.0.0.2:8000"
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
use crate::utils::parceyaml::load_configuration;
|
||||
use crate::utils::structs::{Configuration, ServiceMapping, UpstreamsDashMap};
|
||||
use crate::utils::structs::{Configuration, InnerMap, ServiceMapping, UpstreamsDashMap};
|
||||
use crate::utils::tools::{clone_dashmap_into, compare_dashmaps};
|
||||
use dashmap::DashMap;
|
||||
use futures::channel::mpsc::Sender;
|
||||
@@ -109,7 +109,7 @@ async fn consul_request(url: String, whitelist: Option<Vec<ServiceMapping>>, tok
|
||||
Some(upstreams)
|
||||
}
|
||||
|
||||
async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<String, (Vec<(String, u16, bool, bool, bool)>, AtomicUsize)>> {
|
||||
async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<String, (Vec<InnerMap>, AtomicUsize)>> {
|
||||
let client = reqwest::Client::new();
|
||||
let mut headers = HeaderMap::new();
|
||||
if let Some(token) = token {
|
||||
@@ -118,7 +118,7 @@ async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<Strin
|
||||
let to = Duration::from_secs(1);
|
||||
let u = client.get(url).timeout(to).send();
|
||||
let mut values = Vec::new();
|
||||
let upstreams: DashMap<String, (Vec<(String, u16, bool, bool, bool)>, AtomicUsize)> = DashMap::new();
|
||||
let upstreams: DashMap<String, (Vec<InnerMap>, AtomicUsize)> = DashMap::new();
|
||||
match u.await {
|
||||
Ok(r) => {
|
||||
let jason = r.json::<Vec<Service>>().await;
|
||||
@@ -127,7 +127,14 @@ async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<Strin
|
||||
for service in whitelist {
|
||||
let addr = service.tagged_addresses.get("lan_ipv4").unwrap().address.clone();
|
||||
let prt = service.tagged_addresses.get("lan_ipv4").unwrap().port.clone();
|
||||
let to_add = (addr, prt, false, false, false);
|
||||
let to_add = InnerMap {
|
||||
address: addr,
|
||||
port: prt,
|
||||
is_ssl: false,
|
||||
is_http2: false,
|
||||
to_https: false,
|
||||
rate_limit: None,
|
||||
};
|
||||
values.push(to_add);
|
||||
}
|
||||
}
|
||||
|
||||
@@ -9,6 +9,7 @@ pub struct FromFileProvider {
|
||||
pub path: String,
|
||||
}
|
||||
pub struct APIUpstreamProvider {
|
||||
pub config_api_enabled: bool,
|
||||
pub address: String,
|
||||
pub masterkey: String,
|
||||
pub tls_address: Option<String>,
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
use crate::utils::structs::{UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::utils::structs::{InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::utils::tools::*;
|
||||
use dashmap::DashMap;
|
||||
use log::{error, info, warn};
|
||||
@@ -9,9 +9,11 @@ use std::time::Duration;
|
||||
use tokio::time::interval;
|
||||
use tonic::transport::Endpoint;
|
||||
|
||||
#[allow(unused_assignments)]
|
||||
pub async fn hc2(upslist: Arc<UpstreamsDashMap>, fullist: Arc<UpstreamsDashMap>, idlist: Arc<UpstreamsIdMap>, params: (&str, u64)) {
|
||||
let mut period = interval(Duration::from_secs(params.1));
|
||||
let mut first_run = 0;
|
||||
let client = Client::builder().timeout(Duration::from_secs(2)).danger_accept_invalid_certs(true).build().unwrap();
|
||||
loop {
|
||||
tokio::select! {
|
||||
_ = period.tick() => {
|
||||
@@ -20,47 +22,44 @@ pub async fn hc2(upslist: Arc<UpstreamsDashMap>, fullist: Arc<UpstreamsDashMap>,
|
||||
for val in fclone.iter() {
|
||||
let host = val.key();
|
||||
let inner = DashMap::new();
|
||||
let mut _scheme: (String, u16, bool, bool, bool) = ("".to_string(), 0, false, false, false);
|
||||
let mut scheme = InnerMap::new();
|
||||
for path_entry in val.value().iter() {
|
||||
// let inner = DashMap::new();
|
||||
let path = path_entry.key();
|
||||
let mut innervec= Vec::new();
|
||||
for k in path_entry.value().0 .iter().enumerate() {
|
||||
let (ip, port, _ssl, _version, _redir) = k.1;
|
||||
let mut _link = String::new();
|
||||
let tls = detect_tls(ip, port).await;
|
||||
let tls = detect_tls(k.1.address.as_str(), &k.1.port, &client).await;
|
||||
let mut is_h2 = false;
|
||||
|
||||
// if tls.1 == Some(Version::HTTP_11) {
|
||||
// println!(" V1: ==> {:?}", tls.1)
|
||||
// }else if tls.1 == Some(Version::HTTP_2) {
|
||||
// is_h2 = true;
|
||||
// println!(" V2: ==> {:?}", tls.1)
|
||||
// }
|
||||
|
||||
if tls.1 == Some(Version::HTTP_2) {
|
||||
is_h2 = true;
|
||||
// println!(" V2: ==> {} ==> {:?}", tls.0, tls.1)
|
||||
}
|
||||
|
||||
match tls.0 {
|
||||
true => _link = format!("https://{}:{}{}", ip, port, path),
|
||||
false => _link = format!("http://{}:{}{}", ip, port, path),
|
||||
true => _link = format!("https://{}:{}{}", k.1.address, k.1.port, path),
|
||||
false => _link = format!("http://{}:{}{}", k.1.address, k.1.port, path),
|
||||
}
|
||||
// if _pref == "https://" {
|
||||
// _scheme = (ip.to_string(), *port, true);
|
||||
// }else {
|
||||
// _scheme = (ip.to_string(), *port, false);
|
||||
// }
|
||||
_scheme = (ip.to_string(), *port, tls.0, is_h2, *_redir);
|
||||
// let link = format!("{}{}:{}{}", _pref, ip, port, path);
|
||||
let resp = http_request(_link.as_str(), params.0, "").await;
|
||||
scheme = InnerMap {
|
||||
address: k.1.address.clone(),
|
||||
port: k.1.port,
|
||||
is_ssl: tls.0,
|
||||
is_http2: is_h2,
|
||||
to_https: k.1.to_https,
|
||||
rate_limit: k.1.rate_limit,
|
||||
};
|
||||
let resp = http_request(_link.as_str(), params.0, "", &client).await;
|
||||
match resp.0 {
|
||||
true => {
|
||||
if resp.1 {
|
||||
_scheme = (ip.to_string(), *port, tls.0, true, *_redir);
|
||||
scheme = InnerMap {
|
||||
address: k.1.address.clone(),
|
||||
port: k.1.port,
|
||||
is_ssl: tls.0,
|
||||
is_http2: is_h2,
|
||||
to_https: k.1.to_https,
|
||||
rate_limit: k.1.rate_limit,
|
||||
};
|
||||
}
|
||||
innervec.push(_scheme.clone());
|
||||
innervec.push(scheme);
|
||||
}
|
||||
false => {
|
||||
warn!("Dead Upstream : {}", _link);
|
||||
@@ -91,33 +90,26 @@ pub async fn hc2(upslist: Arc<UpstreamsDashMap>, fullist: Arc<UpstreamsDashMap>,
|
||||
}
|
||||
}
|
||||
|
||||
#[allow(dead_code)]
|
||||
async fn http_request(url: &str, method: &str, payload: &str) -> (bool, bool) {
|
||||
let client = Client::builder().danger_accept_invalid_certs(true).build().unwrap();
|
||||
let timeout = Duration::from_secs(1);
|
||||
async fn http_request(url: &str, method: &str, payload: &str, client: &Client) -> (bool, bool) {
|
||||
if !["POST", "GET", "HEAD"].contains(&method) {
|
||||
error!("Method {} not supported. Only GET|POST|HEAD are supported ", method);
|
||||
return (false, false);
|
||||
}
|
||||
async fn send_request(client: &Client, method: &str, url: &str, payload: &str, timeout: Duration) -> Option<reqwest::Response> {
|
||||
async fn send_request(client: &Client, method: &str, url: &str, payload: &str) -> Option<reqwest::Response> {
|
||||
match method {
|
||||
"POST" => client.post(url).body(payload.to_owned()).timeout(timeout).send().await.ok(),
|
||||
"GET" => client.get(url).timeout(timeout).send().await.ok(),
|
||||
"HEAD" => client.head(url).timeout(timeout).send().await.ok(),
|
||||
"POST" => client.post(url).body(payload.to_owned()).send().await.ok(),
|
||||
"GET" => client.get(url).send().await.ok(),
|
||||
"HEAD" => client.head(url).send().await.ok(),
|
||||
_ => None,
|
||||
}
|
||||
}
|
||||
|
||||
match send_request(&client, method, url, payload, timeout).await {
|
||||
match send_request(&client, method, url, payload).await {
|
||||
Some(response) => {
|
||||
let status = response.status().as_u16();
|
||||
((99..499).contains(&status), false)
|
||||
}
|
||||
None => {
|
||||
// let fallback_url = url.replace("https", "http");
|
||||
// ping_grpc(&fallback_url).await
|
||||
(ping_grpc(&url).await, true)
|
||||
}
|
||||
None => (ping_grpc(&url).await, true),
|
||||
}
|
||||
}
|
||||
|
||||
@@ -128,10 +120,7 @@ pub async fn ping_grpc(addr: &str) -> bool {
|
||||
let endpoint = endpoint.timeout(Duration::from_secs(2));
|
||||
|
||||
match tokio::time::timeout(Duration::from_secs(3), endpoint.connect()).await {
|
||||
Ok(Ok(_channel)) => {
|
||||
// println!("{:?} ==> {:?} ==> {}", endpoint, _channel, addr);
|
||||
true
|
||||
}
|
||||
Ok(Ok(_channel)) => true,
|
||||
_ => false,
|
||||
}
|
||||
} else {
|
||||
@@ -139,15 +128,24 @@ pub async fn ping_grpc(addr: &str) -> bool {
|
||||
}
|
||||
}
|
||||
|
||||
async fn detect_tls(ip: &str, port: &u16) -> (bool, Option<Version>) {
|
||||
let url = format!("https://{}:{}", ip, port);
|
||||
// let url = format!("{}:{}", ip, port);
|
||||
let client = Client::builder().timeout(Duration::from_secs(2)).danger_accept_invalid_certs(true).build().unwrap();
|
||||
match client.get(&url).send().await {
|
||||
Ok(response) => (true, Some(response.version())),
|
||||
Err(e) => {
|
||||
if e.is_builder() || e.is_connect() || e.to_string().contains("tls") {
|
||||
(false, None)
|
||||
async fn detect_tls(ip: &str, port: &u16, client: &Client) -> (bool, Option<Version>) {
|
||||
let https_url = format!("https://{}:{}", ip, port);
|
||||
match client.get(&https_url).send().await {
|
||||
Ok(response) => {
|
||||
// println!("{} => {:?} (HTTPS)", https_url, response.version());
|
||||
return (true, Some(response.version()));
|
||||
}
|
||||
_ => {}
|
||||
}
|
||||
let http_url = format!("http://{}:{}", ip, port);
|
||||
match client.get(&http_url).send().await {
|
||||
Ok(response) => {
|
||||
// println!("{} => {:?} (HTTP)", http_url, response.version());
|
||||
(false, Some(response.version()))
|
||||
}
|
||||
Err(_) => {
|
||||
if ping_grpc(&http_url).await {
|
||||
(false, Some(Version::HTTP_2))
|
||||
} else {
|
||||
(false, None)
|
||||
}
|
||||
|
||||
@@ -1,133 +1,153 @@
|
||||
use crate::utils::structs::*;
|
||||
use dashmap::DashMap;
|
||||
use log::{error, info, warn};
|
||||
use serde_yaml::Error;
|
||||
use std::collections::HashMap;
|
||||
use std::fs;
|
||||
use std::sync::atomic::AtomicUsize;
|
||||
|
||||
pub fn load_configuration(d: &str, kind: &str) -> Option<Configuration> {
|
||||
let mut toreturn: Configuration = Configuration {
|
||||
upstreams: Default::default(),
|
||||
headers: Default::default(),
|
||||
consul: None,
|
||||
typecfg: "".to_string(),
|
||||
extraparams: Extraparams {
|
||||
sticky_sessions: false,
|
||||
to_https: None,
|
||||
authentication: DashMap::new(),
|
||||
let yaml_data = match kind {
|
||||
"filepath" => match fs::read_to_string(d) {
|
||||
Ok(data) => {
|
||||
info!("Reading upstreams from {}", d);
|
||||
data
|
||||
}
|
||||
Err(e) => {
|
||||
error!("Reading: {}: {:?}", d, e);
|
||||
warn!("Running with empty upstreams list, update it via API");
|
||||
return None;
|
||||
}
|
||||
},
|
||||
};
|
||||
toreturn.upstreams = UpstreamsDashMap::new();
|
||||
toreturn.headers = Headers::new();
|
||||
|
||||
let mut yaml_data = d.to_string();
|
||||
match kind {
|
||||
"filepath" => {
|
||||
let _ = match fs::read_to_string(d) {
|
||||
Ok(data) => {
|
||||
info!("Reading upstreams from {}", d);
|
||||
yaml_data = data
|
||||
}
|
||||
Err(e) => {
|
||||
error!("Reading: {}: {:?}", d, e.to_string());
|
||||
warn!("Running with empty upstreams list, update it via API");
|
||||
return None;
|
||||
}
|
||||
};
|
||||
}
|
||||
"content" => {
|
||||
info!("Reading upstreams from API post body");
|
||||
d.to_string()
|
||||
}
|
||||
_ => error!("Mismatched parameter, only filepath|content is allowed "),
|
||||
}
|
||||
|
||||
let p: Result<Config, Error> = serde_yaml::from_str(&yaml_data);
|
||||
match p {
|
||||
Ok(parsed) => {
|
||||
let global_headers = DashMap::new();
|
||||
let mut hl = Vec::new();
|
||||
if let Some(headers) = &parsed.headers {
|
||||
for header in headers.iter() {
|
||||
if let Some((key, val)) = header.split_once(':') {
|
||||
hl.push((key.to_string(), val.to_string()));
|
||||
}
|
||||
}
|
||||
global_headers.insert("/".to_string(), hl);
|
||||
toreturn.headers.insert("GLOBAL_HEADERS".to_string(), global_headers);
|
||||
|
||||
toreturn.extraparams.sticky_sessions = parsed.sticky_sessions;
|
||||
toreturn.extraparams.to_https = parsed.to_https;
|
||||
}
|
||||
if let Some(auth) = &parsed.authorization {
|
||||
let name = auth.get("type").unwrap().to_string();
|
||||
let creds = auth.get("creds").unwrap().to_string();
|
||||
let val: Vec<String> = vec![name, creds];
|
||||
toreturn.extraparams.authentication.insert("authorization".to_string(), val);
|
||||
} else {
|
||||
toreturn.extraparams.authentication = DashMap::new();
|
||||
}
|
||||
|
||||
match parsed.provider.as_str() {
|
||||
"file" => {
|
||||
toreturn.typecfg = "file".to_string();
|
||||
if let Some(upstream) = parsed.upstreams {
|
||||
for (hostname, host_config) in upstream {
|
||||
let path_map = DashMap::new();
|
||||
let header_list = DashMap::new();
|
||||
for (path, path_config) in host_config.paths {
|
||||
let mut server_list = Vec::new();
|
||||
let mut hl = Vec::new();
|
||||
if let Some(headers) = &path_config.headers {
|
||||
for header in headers.iter().by_ref() {
|
||||
if let Some((key, val)) = header.split_once(':') {
|
||||
hl.push((key.to_string(), val.to_string()));
|
||||
}
|
||||
}
|
||||
}
|
||||
header_list.insert(path.clone(), hl);
|
||||
for server in path_config.servers {
|
||||
if let Some((ip, port_str)) = server.split_once(':') {
|
||||
if let Ok(port) = port_str.parse::<u16>() {
|
||||
// let to_https = matches!(path_config.to_https, Some(true));
|
||||
let to_https = path_config.to_https.unwrap_or(false);
|
||||
server_list.push((ip.to_string(), port, true, false, to_https));
|
||||
}
|
||||
}
|
||||
}
|
||||
path_map.insert(path, (server_list, AtomicUsize::new(0)));
|
||||
}
|
||||
toreturn.headers.insert(hostname.clone(), header_list);
|
||||
toreturn.upstreams.insert(hostname, path_map);
|
||||
}
|
||||
}
|
||||
Some(toreturn)
|
||||
}
|
||||
"consul" => {
|
||||
toreturn.typecfg = "consul".to_string();
|
||||
let consul = parsed.consul;
|
||||
match consul {
|
||||
Some(consul) => {
|
||||
toreturn.consul = Some(consul);
|
||||
Some(toreturn)
|
||||
}
|
||||
None => None,
|
||||
}
|
||||
}
|
||||
"kubernetes" => None,
|
||||
_ => {
|
||||
warn!("Unknown provider {}", parsed.provider);
|
||||
None
|
||||
}
|
||||
}
|
||||
_ => {
|
||||
error!("Mismatched parameter, only filepath|content is allowed");
|
||||
return None;
|
||||
}
|
||||
};
|
||||
|
||||
let parsed: Config = match serde_yaml::from_str(&yaml_data) {
|
||||
Ok(cfg) => cfg,
|
||||
Err(e) => {
|
||||
error!("Failed to parse upstreams file: {}", e);
|
||||
return None;
|
||||
}
|
||||
};
|
||||
|
||||
let mut toreturn = Configuration::default();
|
||||
|
||||
populate_headers_and_auth(&mut toreturn, &parsed);
|
||||
toreturn.typecfg = parsed.provider.clone();
|
||||
|
||||
match parsed.provider.as_str() {
|
||||
"file" => {
|
||||
populate_file_upstreams(&mut toreturn, &parsed);
|
||||
Some(toreturn)
|
||||
}
|
||||
"consul" => {
|
||||
toreturn.consul = parsed.consul;
|
||||
if toreturn.consul.is_some() {
|
||||
Some(toreturn)
|
||||
} else {
|
||||
None
|
||||
}
|
||||
}
|
||||
"kubernetes" => None,
|
||||
_ => {
|
||||
warn!("Unknown provider {}", parsed.provider);
|
||||
None
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
fn populate_headers_and_auth(config: &mut Configuration, parsed: &Config) {
|
||||
if let Some(headers) = &parsed.headers {
|
||||
let mut hl = Vec::new();
|
||||
for header in headers {
|
||||
if let Some((key, val)) = header.split_once(':') {
|
||||
hl.push((key.trim().to_string(), val.trim().to_string()));
|
||||
}
|
||||
}
|
||||
|
||||
let global_headers = DashMap::new();
|
||||
global_headers.insert("/".to_string(), hl);
|
||||
config.headers.insert("GLOBAL_HEADERS".to_string(), global_headers);
|
||||
}
|
||||
|
||||
config.extraparams.sticky_sessions = parsed.sticky_sessions;
|
||||
config.extraparams.to_https = parsed.to_https;
|
||||
config.extraparams.rate_limit = parsed.rate_limit;
|
||||
|
||||
if let Some(rate) = &parsed.rate_limit {
|
||||
info!("Applied Global Rate Limit : {} request per second", rate);
|
||||
}
|
||||
|
||||
if let Some(auth) = &parsed.authorization {
|
||||
let name = auth.get("type").unwrap_or(&"".to_string()).to_string();
|
||||
let creds = auth.get("creds").unwrap_or(&"".to_string()).to_string();
|
||||
config.extraparams.authentication.insert("authorization".to_string(), vec![name, creds]);
|
||||
} else {
|
||||
config.extraparams.authentication = DashMap::new();
|
||||
}
|
||||
}
|
||||
|
||||
fn populate_file_upstreams(config: &mut Configuration, parsed: &Config) {
|
||||
if let Some(upstreams) = &parsed.upstreams {
|
||||
for (hostname, host_config) in upstreams {
|
||||
let path_map = DashMap::new();
|
||||
let header_list = DashMap::new();
|
||||
for (path, path_config) in &host_config.paths {
|
||||
if let Some(rate) = &path_config.rate_limit {
|
||||
info!("Applied Rate Limit for {} : {} request per second", hostname, rate);
|
||||
}
|
||||
|
||||
let mut server_list = Vec::new();
|
||||
let mut hl = Vec::new();
|
||||
|
||||
if let Some(headers) = &path_config.headers {
|
||||
for header in headers {
|
||||
if let Some((key, val)) = header.split_once(':') {
|
||||
hl.push((key.trim().to_string(), val.trim().to_string()));
|
||||
}
|
||||
}
|
||||
}
|
||||
header_list.insert(path.clone(), hl);
|
||||
|
||||
for server in &path_config.servers {
|
||||
// let mut rate: Option<isize> = None;
|
||||
// let size: isize = path_config.servers.len() as isize;
|
||||
// if let Some(limit) = &path_config.rate_limit {
|
||||
// if size > 0 {
|
||||
// rate = Some(limit / size);
|
||||
// }
|
||||
// }
|
||||
|
||||
if let Some((ip, port_str)) = server.split_once(':') {
|
||||
if let Ok(port) = port_str.parse::<u16>() {
|
||||
server_list.push(InnerMap {
|
||||
address: ip.trim().to_string(),
|
||||
port,
|
||||
is_ssl: true,
|
||||
is_http2: false,
|
||||
to_https: path_config.to_https.unwrap_or(false),
|
||||
// rate_limit: rate,
|
||||
rate_limit: path_config.rate_limit,
|
||||
});
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
path_map.insert(path.clone(), (server_list, AtomicUsize::new(0)));
|
||||
}
|
||||
|
||||
config.headers.insert(hostname.clone(), header_list);
|
||||
config.upstreams.insert(hostname.clone(), path_map);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
pub fn parce_main_config(path: &str) -> AppConfig {
|
||||
info!("Parsing configuration");
|
||||
let data = fs::read_to_string(path).unwrap();
|
||||
|
||||
@@ -3,54 +3,81 @@ use serde::{Deserialize, Serialize};
|
||||
use std::collections::HashMap;
|
||||
use std::sync::atomic::AtomicUsize;
|
||||
|
||||
pub type InnerMap = (String, u16, bool, bool, bool);
|
||||
// pub type InnerMap = BackendConfig;
|
||||
pub type UpstreamsDashMap = DashMap<String, DashMap<String, (Vec<InnerMap>, AtomicUsize)>>;
|
||||
|
||||
// #[derive(Debug, Default)]
|
||||
// pub struct UpstreamsMap {
|
||||
// pub upstreams: DashMap<String, DashMap<String, (Vec<InnerMap>, AtomicUsize)>>,
|
||||
// pub ratelimit: DashMap<String, Option<isize>>,
|
||||
// }
|
||||
// impl UpstreamsMap {
|
||||
// pub fn new() -> Self {
|
||||
// Self {
|
||||
// upstreams: Default::default(),
|
||||
// ratelimit: Default::default(),
|
||||
// }
|
||||
// }
|
||||
// }
|
||||
//
|
||||
// pub type XUpstreamsDashMap = DashMap<String, UpstreamsMap>;
|
||||
|
||||
pub type UpstreamsIdMap = DashMap<String, InnerMap>;
|
||||
pub type Headers = DashMap<String, DashMap<String, Vec<(String, String)>>>;
|
||||
|
||||
#[derive(Debug, Clone, Serialize, Deserialize)]
|
||||
#[derive(Debug, Default, Clone, Serialize, Deserialize)]
|
||||
pub struct ServiceMapping {
|
||||
pub proxy: String,
|
||||
pub real: String,
|
||||
}
|
||||
|
||||
#[derive(Clone, Debug)]
|
||||
#[derive(Clone, Debug, Default)]
|
||||
pub struct Extraparams {
|
||||
pub sticky_sessions: bool,
|
||||
pub to_https: Option<bool>,
|
||||
pub authentication: DashMap<String, Vec<String>>,
|
||||
pub rate_limit: Option<isize>,
|
||||
}
|
||||
|
||||
#[derive(Clone, Debug, Serialize, Deserialize)]
|
||||
#[derive(Clone, Default, Debug, Serialize, Deserialize)]
|
||||
pub struct Consul {
|
||||
pub servers: Option<Vec<String>>,
|
||||
pub services: Option<Vec<ServiceMapping>>,
|
||||
pub token: Option<String>,
|
||||
}
|
||||
#[derive(Debug, Serialize, Deserialize)]
|
||||
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||
pub struct Config {
|
||||
pub provider: String,
|
||||
pub sticky_sessions: bool,
|
||||
pub to_https: Option<bool>,
|
||||
#[serde(default)]
|
||||
pub upstreams: Option<HashMap<String, HostConfig>>,
|
||||
#[serde(default)]
|
||||
pub globals: Option<HashMap<String, Vec<String>>>,
|
||||
#[serde(default)]
|
||||
pub headers: Option<Vec<String>>,
|
||||
#[serde(default)]
|
||||
pub authorization: Option<HashMap<String, String>>,
|
||||
#[serde(default)]
|
||||
pub consul: Option<Consul>,
|
||||
#[serde(default)]
|
||||
pub rate_limit: Option<isize>,
|
||||
}
|
||||
|
||||
#[derive(Debug, Serialize, Deserialize)]
|
||||
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||
pub struct HostConfig {
|
||||
pub paths: HashMap<String, PathConfig>,
|
||||
pub rate_limit: Option<isize>,
|
||||
}
|
||||
|
||||
#[derive(Debug, Serialize, Deserialize)]
|
||||
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||
pub struct PathConfig {
|
||||
pub servers: Vec<String>,
|
||||
pub to_https: Option<bool>,
|
||||
pub headers: Option<Vec<String>>,
|
||||
pub rate_limit: Option<isize>,
|
||||
}
|
||||
#[derive(Debug)]
|
||||
#[derive(Debug, Default)]
|
||||
pub struct Configuration {
|
||||
pub upstreams: UpstreamsDashMap,
|
||||
pub headers: Headers,
|
||||
@@ -59,7 +86,7 @@ pub struct Configuration {
|
||||
pub extraparams: Extraparams,
|
||||
}
|
||||
|
||||
#[derive(Debug, Deserialize)]
|
||||
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||
pub struct AppConfig {
|
||||
pub hc_interval: u16,
|
||||
pub hc_method: String,
|
||||
@@ -68,6 +95,7 @@ pub struct AppConfig {
|
||||
pub master_key: String,
|
||||
pub config_address: String,
|
||||
pub proxy_address_http: String,
|
||||
pub config_api_enabled: bool,
|
||||
pub config_tls_address: Option<String>,
|
||||
pub config_tls_certificate: Option<String>,
|
||||
pub config_tls_key_file: Option<String>,
|
||||
@@ -78,3 +106,26 @@ pub struct AppConfig {
|
||||
pub file_server_address: Option<String>,
|
||||
pub file_server_folder: Option<String>,
|
||||
}
|
||||
|
||||
#[derive(Debug, Clone, PartialEq, Eq, Hash)]
|
||||
pub struct InnerMap {
|
||||
pub address: String,
|
||||
pub port: u16,
|
||||
pub is_ssl: bool,
|
||||
pub is_http2: bool,
|
||||
pub to_https: bool,
|
||||
pub rate_limit: Option<isize>,
|
||||
}
|
||||
|
||||
impl InnerMap {
|
||||
pub fn new() -> Self {
|
||||
Self {
|
||||
address: Default::default(),
|
||||
port: Default::default(),
|
||||
is_ssl: Default::default(),
|
||||
is_http2: Default::default(),
|
||||
to_https: Default::default(),
|
||||
rate_limit: Default::default(),
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
use crate::utils::structs::{UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::utils::structs::{InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::utils::tls;
|
||||
use crate::utils::tls::CertificateConfig;
|
||||
use dashmap::DashMap;
|
||||
@@ -21,10 +21,12 @@ pub fn print_upstreams(upstreams: &UpstreamsDashMap) {
|
||||
|
||||
for path_entry in host_entry.value().iter() {
|
||||
let path = path_entry.key();
|
||||
println!(" Path: {}", path);
|
||||
|
||||
for (ip, port, ssl, vers, to_https) in path_entry.value().0.clone() {
|
||||
println!(" ===> IP: {}, Port: {}, SSL: {}, H2: {}, To HTTPS: {}", ip, port, ssl, vers, to_https);
|
||||
println!(" Path: {}", path);
|
||||
for f in path_entry.value().0.clone() {
|
||||
println!(
|
||||
" IP: {}, Port: {}, SSL: {}, H2: {}, To HTTPS: {}",
|
||||
f.address, f.port, f.is_ssl, f.is_http2, f.to_https
|
||||
);
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -140,13 +142,21 @@ pub fn clone_idmap_into(original: &UpstreamsDashMap, cloned: &UpstreamsIdMap) {
|
||||
let new_vec = vec.clone();
|
||||
for x in vec.iter() {
|
||||
let mut id = String::new();
|
||||
write!(&mut id, "{}:{}:{}", x.0, x.1, x.2).unwrap();
|
||||
write!(&mut id, "{}:{}:{}", x.address, x.port, x.is_ssl).unwrap();
|
||||
let mut hasher = Sha256::new();
|
||||
hasher.update(id.clone().into_bytes());
|
||||
let hash = hasher.finalize();
|
||||
let hex_hash = base16ct::lower::encode_string(&hash);
|
||||
let hh = hex_hash[0..50].to_string();
|
||||
cloned.insert(id, (hh.clone(), 0000, false, false, false));
|
||||
let to_add = InnerMap {
|
||||
address: hh.clone(),
|
||||
port: 0,
|
||||
is_ssl: false,
|
||||
is_http2: false,
|
||||
to_https: false,
|
||||
rate_limit: None,
|
||||
};
|
||||
cloned.insert(id, to_add);
|
||||
cloned.insert(hh, x.to_owned());
|
||||
}
|
||||
new_inner_map.insert(path.clone(), new_vec);
|
||||
|
||||
@@ -36,6 +36,7 @@ impl BackgroundService for LB {
|
||||
let api_load = APIUpstreamProvider {
|
||||
address: self.config.config_address.clone(),
|
||||
masterkey: self.config.master_key.clone(),
|
||||
config_api_enabled: self.config.config_api_enabled.clone(),
|
||||
tls_address: self.config.config_tls_address.clone(),
|
||||
tls_certificate: self.config.config_tls_certificate.clone(),
|
||||
tls_key_file: self.config.config_tls_key_file.clone(),
|
||||
@@ -66,6 +67,7 @@ impl BackgroundService for LB {
|
||||
new.sticky_sessions = ss.extraparams.sticky_sessions;
|
||||
new.to_https = ss.extraparams.to_https;
|
||||
new.authentication = ss.extraparams.authentication.clone();
|
||||
new.rate_limit = ss.extraparams.rate_limit;
|
||||
self.extraparams.store(Arc::new(new));
|
||||
self.headers.clear();
|
||||
|
||||
|
||||
@@ -45,7 +45,6 @@ impl GetHost for LB {
|
||||
}
|
||||
}
|
||||
}
|
||||
// println!("BMT :===> {:?}", best_match);
|
||||
best_match
|
||||
}
|
||||
fn get_header(&self, peer: &str, path: &str) -> Option<Vec<(String, String)>> {
|
||||
|
||||
@@ -1,20 +1,25 @@
|
||||
use crate::utils::auth::authenticate;
|
||||
use crate::utils::metrics::*;
|
||||
use crate::utils::structs::{AppConfig, Extraparams, Headers, UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::utils::structs::{AppConfig, Extraparams, Headers, InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||
use crate::web::gethosts::GetHost;
|
||||
use arc_swap::ArcSwap;
|
||||
use async_trait::async_trait;
|
||||
use axum::body::Bytes;
|
||||
use log::{debug, warn};
|
||||
use once_cell::sync::Lazy;
|
||||
use pingora::http::{RequestHeader, ResponseHeader, StatusCode};
|
||||
use pingora::prelude::*;
|
||||
use pingora::ErrorSource::Upstream;
|
||||
use pingora_core::listeners::ALPN;
|
||||
use pingora_core::prelude::HttpPeer;
|
||||
use pingora_limits::rate::Rate;
|
||||
use pingora_proxy::{ProxyHttp, Session};
|
||||
use std::sync::Arc;
|
||||
use std::time::Duration;
|
||||
use tokio::time::Instant;
|
||||
|
||||
static RATE_LIMITER: Lazy<Rate> = Lazy::new(|| Rate::new(Duration::from_secs(1)));
|
||||
|
||||
#[derive(Clone)]
|
||||
pub struct LB {
|
||||
pub ump_upst: Arc<UpstreamsDashMap>,
|
||||
@@ -30,6 +35,9 @@ pub struct Context {
|
||||
to_https: bool,
|
||||
redirect_to: String,
|
||||
start_time: Instant,
|
||||
hostname: Option<String>,
|
||||
upstream_peer: Option<InnerMap>,
|
||||
extraparams: arc_swap::Guard<Arc<Extraparams>>,
|
||||
}
|
||||
|
||||
#[async_trait]
|
||||
@@ -41,55 +49,89 @@ impl ProxyHttp for LB {
|
||||
to_https: false,
|
||||
redirect_to: String::new(),
|
||||
start_time: Instant::now(),
|
||||
hostname: None,
|
||||
upstream_peer: None,
|
||||
extraparams: self.extraparams.load(),
|
||||
}
|
||||
}
|
||||
async fn request_filter(&self, session: &mut Session, _ctx: &mut Self::CTX) -> Result<bool> {
|
||||
if let Some(auth) = self.extraparams.load().authentication.get("authorization") {
|
||||
let ep = _ctx.extraparams.clone();
|
||||
|
||||
if let Some(auth) = ep.authentication.get("authorization") {
|
||||
let authenticated = authenticate(&auth.value(), &session);
|
||||
if !authenticated {
|
||||
let _ = session.respond_error(401).await;
|
||||
warn!("Forbidden: {:?}, {}", session.client_addr(), session.req_header().uri.path().to_string());
|
||||
warn!("Forbidden: {:?}, {}", session.client_addr(), session.req_header().uri.path());
|
||||
return Ok(true);
|
||||
}
|
||||
};
|
||||
Ok(false)
|
||||
}
|
||||
async fn upstream_peer(&self, session: &mut Session, ctx: &mut Self::CTX) -> Result<Box<HttpPeer>> {
|
||||
let host_name = return_header_host(&session);
|
||||
match host_name {
|
||||
Some(hostname) => {
|
||||
let mut backend_id = None;
|
||||
|
||||
if self.extraparams.load().sticky_sessions {
|
||||
if let Some(cookies) = session.req_header().headers.get("cookie") {
|
||||
if let Ok(cookie_str) = cookies.to_str() {
|
||||
for cookie in cookie_str.split(';') {
|
||||
let trimmed = cookie.trim();
|
||||
if let Some(value) = trimmed.strip_prefix("backend_id=") {
|
||||
backend_id = Some(value);
|
||||
break;
|
||||
}
|
||||
let hostname = return_header_host(&session);
|
||||
_ctx.hostname = hostname.clone();
|
||||
|
||||
let mut backend_id = None;
|
||||
|
||||
if ep.sticky_sessions {
|
||||
if let Some(cookies) = session.req_header().headers.get("cookie") {
|
||||
if let Ok(cookie_str) = cookies.to_str() {
|
||||
for cookie in cookie_str.split(';') {
|
||||
let trimmed = cookie.trim();
|
||||
if let Some(value) = trimmed.strip_prefix("backend_id=") {
|
||||
backend_id = Some(value);
|
||||
break;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
match hostname {
|
||||
None => return Ok(false),
|
||||
Some(host) => {
|
||||
let optioninnermap = self.get_host(host.as_str(), host.as_str(), backend_id);
|
||||
match optioninnermap {
|
||||
None => return Ok(false),
|
||||
Some(ref innermap) => {
|
||||
if let Some(rate) = innermap.rate_limit.or(ep.rate_limit) {
|
||||
// let rate_key = session.client_addr().and_then(|addr| addr.as_inet()).map(|inet| inet.ip().to_string()).unwrap_or_else(|| host.to_string());
|
||||
let rate_key = session.client_addr().and_then(|addr| addr.as_inet()).map(|inet| inet.ip());
|
||||
let curr_window_requests = RATE_LIMITER.observe(&rate_key, 1);
|
||||
if curr_window_requests > rate {
|
||||
let mut header = ResponseHeader::build(429, None).unwrap();
|
||||
header.insert_header("X-Rate-Limit-Limit", rate.to_string()).unwrap();
|
||||
header.insert_header("X-Rate-Limit-Remaining", "0").unwrap();
|
||||
header.insert_header("X-Rate-Limit-Reset", "1").unwrap();
|
||||
session.set_keepalive(None);
|
||||
session.write_response_header(Box::new(header), true).await?;
|
||||
debug!("Rate limited: {:?}, {}", rate_key, rate);
|
||||
return Ok(true);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
let ddr = self.get_host(hostname, hostname, backend_id);
|
||||
|
||||
match ddr {
|
||||
Some((address, port, ssl, is_h2, to_https)) => {
|
||||
let mut peer = Box::new(HttpPeer::new((address.clone(), port.clone()), ssl, String::new()));
|
||||
_ctx.upstream_peer = optioninnermap;
|
||||
}
|
||||
}
|
||||
Ok(false)
|
||||
}
|
||||
async fn upstream_peer(&self, session: &mut Session, ctx: &mut Self::CTX) -> Result<Box<HttpPeer>> {
|
||||
// let host_name = return_header_host(&session);
|
||||
match ctx.hostname.as_ref() {
|
||||
Some(hostname) => {
|
||||
match ctx.upstream_peer.as_ref() {
|
||||
// Some((address, port, ssl, is_h2, to_https)) => {
|
||||
Some(innermap) => {
|
||||
let mut peer = Box::new(HttpPeer::new((innermap.address.clone(), innermap.port.clone()), innermap.is_ssl, String::new()));
|
||||
// if session.is_http2() {
|
||||
if is_h2 {
|
||||
if innermap.is_http2 {
|
||||
peer.options.alpn = ALPN::H2;
|
||||
}
|
||||
if ssl {
|
||||
peer.sni = hostname.to_string();
|
||||
if innermap.is_ssl {
|
||||
peer.sni = hostname.clone();
|
||||
peer.options.verify_cert = false;
|
||||
peer.options.verify_hostname = false;
|
||||
}
|
||||
|
||||
if self.extraparams.load().to_https.unwrap_or(false) || to_https {
|
||||
if ctx.to_https || innermap.to_https {
|
||||
if let Some(stream) = session.stream() {
|
||||
if stream.get_ssl().is_none() {
|
||||
if let Some(addr) = session.server_addr() {
|
||||
@@ -104,7 +146,7 @@ impl ProxyHttp for LB {
|
||||
}
|
||||
}
|
||||
|
||||
ctx.backend_id = format!("{}:{}:{}", address.clone(), port.clone(), ssl);
|
||||
ctx.backend_id = format!("{}:{}:{}", innermap.address.clone(), innermap.port.clone(), innermap.is_ssl);
|
||||
Ok(peer)
|
||||
}
|
||||
None => {
|
||||
@@ -160,10 +202,10 @@ impl ProxyHttp for LB {
|
||||
// }
|
||||
async fn response_filter(&self, session: &mut Session, _upstream_response: &mut ResponseHeader, ctx: &mut Self::CTX) -> Result<()> {
|
||||
// _upstream_response.insert_header("X-Proxied-From", "Fooooooooooooooo").unwrap();
|
||||
if self.extraparams.load().sticky_sessions {
|
||||
if ctx.extraparams.sticky_sessions {
|
||||
let backend_id = ctx.backend_id.clone();
|
||||
if let Some(bid) = self.ump_byid.get(&backend_id) {
|
||||
let _ = _upstream_response.insert_header("set-cookie", format!("backend_id={}; Path=/; Max-Age=600; HttpOnly; SameSite=Lax", bid.0));
|
||||
let _ = _upstream_response.insert_header("set-cookie", format!("backend_id={}; Path=/; Max-Age=600; HttpOnly; SameSite=Lax", bid.address));
|
||||
}
|
||||
}
|
||||
if ctx.to_https {
|
||||
@@ -172,7 +214,8 @@ impl ProxyHttp for LB {
|
||||
redirect_response.insert_header("Content-Length", "0")?;
|
||||
session.write_response_header(Box::new(redirect_response), false).await?;
|
||||
}
|
||||
match return_header_host(&session) {
|
||||
// match return_header_host(&session) {
|
||||
match ctx.hostname.as_ref() {
|
||||
Some(host) => {
|
||||
let path = session.req_header().uri.path();
|
||||
let host_header = host;
|
||||
@@ -215,17 +258,17 @@ impl ProxyHttp for LB {
|
||||
}
|
||||
}
|
||||
|
||||
fn return_header_host(session: &Session) -> Option<&str> {
|
||||
fn return_header_host(session: &Session) -> Option<String> {
|
||||
if session.is_http2() {
|
||||
match session.req_header().uri.host() {
|
||||
Some(host) => Option::from(host),
|
||||
Some(host) => Option::from(host.to_string()),
|
||||
None => None,
|
||||
}
|
||||
} else {
|
||||
match session.req_header().headers.get("host") {
|
||||
Some(host) => {
|
||||
let header_host = host.to_str().unwrap().splitn(2, ':').collect::<Vec<&str>>();
|
||||
Option::from(header_host[0])
|
||||
Option::from(header_host[0].to_string())
|
||||
}
|
||||
None => None,
|
||||
}
|
||||
|
||||
@@ -33,6 +33,7 @@ pub fn run() {
|
||||
sticky_sessions: false,
|
||||
to_https: None,
|
||||
authentication: DashMap::new(),
|
||||
rate_limit: None,
|
||||
}));
|
||||
|
||||
let cfg = Arc::new(maincfg);
|
||||
|
||||
@@ -35,6 +35,7 @@ struct OutToken {
|
||||
struct AppState {
|
||||
master_key: String,
|
||||
config_sender: Sender<Configuration>,
|
||||
config_api_enabled: bool,
|
||||
}
|
||||
|
||||
#[allow(unused_mut)]
|
||||
@@ -42,6 +43,7 @@ pub async fn run_server(config: &APIUpstreamProvider, mut to_return: Sender<Conf
|
||||
let app_state = AppState {
|
||||
master_key: config.masterkey.clone(),
|
||||
config_sender: to_return.clone(),
|
||||
config_api_enabled: config.config_api_enabled.clone(),
|
||||
};
|
||||
|
||||
let app = Router::new()
|
||||
@@ -81,8 +83,15 @@ pub async fn run_server(config: &APIUpstreamProvider, mut to_return: Sender<Conf
|
||||
}
|
||||
|
||||
async fn conf(State(mut st): State<AppState>, Query(params): Query<HashMap<String, String>>, content: String) -> impl IntoResponse {
|
||||
if !st.config_api_enabled {
|
||||
return Response::builder()
|
||||
.status(StatusCode::FORBIDDEN)
|
||||
.body(Body::from("Config remote API is disabled !\n"))
|
||||
.unwrap();
|
||||
}
|
||||
|
||||
if let Some(s) = params.get("key") {
|
||||
if s.to_owned() == st.master_key.to_owned() {
|
||||
if s.to_owned() == st.master_key {
|
||||
if let Some(serverlist) = crate::utils::parceyaml::load_configuration(content.as_str(), "content") {
|
||||
st.config_sender.send(serverlist).await.unwrap();
|
||||
return Response::builder().status(StatusCode::OK).body(Body::from("Config, conf file, updated !\n")).unwrap();
|
||||
|
||||
Reference in New Issue
Block a user