mirror of
https://github.com/sadoyan/aralez.git
synced 2026-04-30 14:58:38 +08:00
Compare commits
11 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
d3602fa578 | ||
|
|
e304482667 | ||
|
|
f8118f9596 | ||
|
|
f654312466 | ||
|
|
b44f7069a0 | ||
|
|
a44979ec82 | ||
|
|
ece4fa20af | ||
|
|
2ad3a059ab | ||
|
|
6f012cee69 | ||
|
|
51c88c8f7c | ||
|
|
f91bc41103 |
3
.gitignore
vendored
3
.gitignore
vendored
@@ -5,9 +5,12 @@
|
|||||||
*.dll
|
*.dll
|
||||||
*.exe
|
*.exe
|
||||||
*.sh
|
*.sh
|
||||||
|
/docs/
|
||||||
|
/docs
|
||||||
/target/
|
/target/
|
||||||
*.iml
|
*.iml
|
||||||
.idea/
|
.idea/
|
||||||
|
.etc/
|
||||||
*.ipr
|
*.ipr
|
||||||
*.iws
|
*.iws
|
||||||
/out/
|
/out/
|
||||||
|
|||||||
@@ -48,7 +48,9 @@ lazy_static = "1.5.0"
|
|||||||
#openssl = "0.10.73"
|
#openssl = "0.10.73"
|
||||||
x509-parser = "0.17.0"
|
x509-parser = "0.17.0"
|
||||||
rustls-pemfile = "2.2.0"
|
rustls-pemfile = "2.2.0"
|
||||||
|
#hickory-client = { version = "0.25.2" }
|
||||||
tower-http = { version = "0.6.6", features = ["fs"] }
|
tower-http = { version = "0.6.6", features = ["fs"] }
|
||||||
once_cell = "1.20.2"
|
once_cell = "1.20.2"
|
||||||
|
#moka = { version = "0.12.10", features = ["sync"] }
|
||||||
|
|
||||||
|
|
||||||
|
|||||||
120
METRICS.md
120
METRICS.md
@@ -1,120 +0,0 @@
|
|||||||
# 📈 Aralez Prometheus Metrics Reference
|
|
||||||
|
|
||||||
This document outlines Prometheus metrics for the [Aralez](https://github.com/sadoyan/aralez) reverse proxy.
|
|
||||||
These metrics can be used for monitoring, alerting and performance analysis.
|
|
||||||
|
|
||||||
Exposed to `http://config_address/metrics`
|
|
||||||
|
|
||||||
By default `http://127.0.0.1:3000/metrics`
|
|
||||||
|
|
||||||
# 📊 Example Grafana dashboard during stress test :
|
|
||||||
|
|
||||||

|
|
||||||
|
|
||||||
---
|
|
||||||
|
|
||||||
## 🛠️ Prometheus Metrics
|
|
||||||
|
|
||||||
### 1. `aralez_requests_total`
|
|
||||||
|
|
||||||
- **Type**: `Counter`
|
|
||||||
- **Purpose**: Total amount requests served by Aralez.
|
|
||||||
|
|
||||||
**PromQL example:**
|
|
||||||
|
|
||||||
```promql
|
|
||||||
rate(aralez_requests_total[5m])
|
|
||||||
```
|
|
||||||
|
|
||||||
---
|
|
||||||
|
|
||||||
### 2. `aralez_errors_total`
|
|
||||||
|
|
||||||
- **Type**: `Counter`
|
|
||||||
- **Purpose**: Count of requests that resulted in an error.
|
|
||||||
|
|
||||||
**PromQL example:**
|
|
||||||
|
|
||||||
```promql
|
|
||||||
rate(aralez_errors_total[5m])
|
|
||||||
```
|
|
||||||
|
|
||||||
---
|
|
||||||
|
|
||||||
### 3. `aralez_responses_total{status="200"}`
|
|
||||||
|
|
||||||
- **Type**: `CounterVec`
|
|
||||||
- **Purpose**: Count of responses by HTTP status code.
|
|
||||||
|
|
||||||
**PromQL example:**
|
|
||||||
|
|
||||||
```promql
|
|
||||||
rate(aralez_responses_total{status=~"5.."}[5m]) > 0
|
|
||||||
```
|
|
||||||
|
|
||||||
> Useful for alerting on 5xx errors.
|
|
||||||
|
|
||||||
---
|
|
||||||
|
|
||||||
### 4. `aralez_response_latency_seconds`
|
|
||||||
|
|
||||||
- **Type**: `Histogram`
|
|
||||||
- **Purpose**: Tracks the latency of responses in seconds.
|
|
||||||
|
|
||||||
**Example bucket output:**
|
|
||||||
|
|
||||||
```prometheus
|
|
||||||
aralez_response_latency_seconds_bucket{le="0.01"} 15
|
|
||||||
aralez_response_latency_seconds_bucket{le="0.1"} 120
|
|
||||||
aralez_response_latency_seconds_bucket{le="0.25"} 245
|
|
||||||
aralez_response_latency_seconds_bucket{le="0.5"} 500
|
|
||||||
...
|
|
||||||
aralez_response_latency_seconds_count 1023
|
|
||||||
aralez_response_latency_seconds_sum 42.6
|
|
||||||
```
|
|
||||||
|
|
||||||
| Metric | Meaning |
|
|
||||||
|-------------------------|---------------------------------------------------------------|
|
|
||||||
| `bucket{le="0.1"} 120` | 120 requests were ≤ 100ms |
|
|
||||||
| `bucket{le="0.25"} 245` | 245 requests were ≤ 250ms |
|
|
||||||
| `count` | Total number of observations (i.e., total responses measured) |
|
|
||||||
| `sum` | Total time of all responses, in seconds |
|
|
||||||
|
|
||||||
### 🔍 How to interpret:
|
|
||||||
|
|
||||||
- `le` means “less than or equal to”.
|
|
||||||
- `count` is total amount of observations.
|
|
||||||
- `sum` is the total time (in seconds) of all responses.
|
|
||||||
|
|
||||||
**PromQL examples:**
|
|
||||||
|
|
||||||
🔹 **95th percentile latency**
|
|
||||||
|
|
||||||
```promql
|
|
||||||
histogram_quantile(0.95, rate(aralez_response_latency_seconds_bucket[5m]))
|
|
||||||
|
|
||||||
```
|
|
||||||
|
|
||||||
🔹 **Average latency**
|
|
||||||
|
|
||||||
```promql
|
|
||||||
rate(aralez_response_latency_seconds_sum[5m]) / rate(aralez_response_latency_seconds_count[5m])
|
|
||||||
```
|
|
||||||
|
|
||||||
---
|
|
||||||
|
|
||||||
## ✅ Notes
|
|
||||||
|
|
||||||
- Metrics are registered after the first served request.
|
|
||||||
|
|
||||||
---
|
|
||||||
✅ Summary of key metrics
|
|
||||||
|
|
||||||
| Metric Name | Type | What it Tells You |
|
|
||||||
|---------------------------------------|------------|---------------------------|
|
|
||||||
| `aralez_requests_total` | Counter | Total requests served |
|
|
||||||
| `aralez_errors_total` | Counter | Number of failed requests |
|
|
||||||
| `aralez_responses_total{status="200"}` | CounterVec | Response status breakdown |
|
|
||||||
| `aralez_response_latency_seconds` | Histogram | How fast responses are |
|
|
||||||
|
|
||||||
📘 *Last updated: May 2025*
|
|
||||||
74
README.md
74
README.md
@@ -16,6 +16,8 @@ Built on Rust, on top of **Cloudflare’s Pingora engine**, **Aralez** delivers
|
|||||||
- **Automatic load of certificates** — Automatically reads and loads certificates from a folder, without a restart.
|
- **Automatic load of certificates** — Automatically reads and loads certificates from a folder, without a restart.
|
||||||
- **Upstreams TLS detection** — Aralez will automatically detect if upstreams uses secure connection.
|
- **Upstreams TLS detection** — Aralez will automatically detect if upstreams uses secure connection.
|
||||||
- **Built in rate limiter** — Limit requests to server, by setting up upper limit for requests per seconds, per virtualhost.
|
- **Built in rate limiter** — Limit requests to server, by setting up upper limit for requests per seconds, per virtualhost.
|
||||||
|
- **Global rate limiter** — Set rate limit for all virtualhosts.
|
||||||
|
- **Per path rate limiter** — Set rate limit for specific paths. Path limits will override global limits.
|
||||||
- **Authentication** — Supports Basic Auth, API tokens, and JWT verification.
|
- **Authentication** — Supports Basic Auth, API tokens, and JWT verification.
|
||||||
- **Basic Auth**
|
- **Basic Auth**
|
||||||
- **API Key** via `x-api-key` header
|
- **API Key** via `x-api-key` header
|
||||||
@@ -64,31 +66,32 @@ Built on Rust, on top of **Cloudflare’s Pingora engine**, **Aralez** delivers
|
|||||||
|
|
||||||
### 🔧 `main.yaml`
|
### 🔧 `main.yaml`
|
||||||
|
|
||||||
| Key | Example Value | Description |
|
| Key | Example Value | Description |
|
||||||
|----------------------------------|--------------------------------------|--------------------------------------------------------------------------------------------------|
|
|----------------------------------|--------------------------------------|----------------------------------------------------------------------------------------------------|
|
||||||
| **threads** | 12 | Number of running daemon threads. Optional, defaults to 1 |
|
| **threads** | 12 | Number of running daemon threads. Optional, defaults to 1 |
|
||||||
| **user** | aralez | Optional, Username for running aralez after dropping root privileges, requires to launch as root |
|
| **user** | aralez | Optional, Username for running aralez after dropping root privileges, requires to launch as root |
|
||||||
| **group** | aralez | Optional,Group for running aralez after dropping root privileges, requires to launch as root |
|
| **group** | aralez | Optional,Group for running aralez after dropping root privileges, requires to launch as root |
|
||||||
| **daemon** | false | Run in background (boolean) |
|
| **daemon** | false | Run in background (boolean) |
|
||||||
| **upstream_keepalive_pool_size** | 500 | Pool size for upstream keepalive connections |
|
| **upstream_keepalive_pool_size** | 500 | Pool size for upstream keepalive connections |
|
||||||
| **pid_file** | /tmp/aralez.pid | Path to PID file |
|
| **pid_file** | /tmp/aralez.pid | Path to PID file |
|
||||||
| **error_log** | /tmp/aralez_err.log | Path to error log file |
|
| **error_log** | /tmp/aralez_err.log | Path to error log file |
|
||||||
| **upgrade_sock** | /tmp/aralez.sock | Path to live upgrade socket file |
|
| **upgrade_sock** | /tmp/aralez.sock | Path to live upgrade socket file |
|
||||||
| **config_address** | 0.0.0.0:3000 | HTTP API address for pushing upstreams.yaml from remote location |
|
| **config_address** | 0.0.0.0:3000 | HTTP API address for pushing upstreams.yaml from remote location |
|
||||||
| **config_tls_address** | 0.0.0.0:3001 | HTTPS API address for pushing upstreams.yaml from remote location |
|
| **config_tls_address** | 0.0.0.0:3001 | HTTPS API address for pushing upstreams.yaml from remote location |
|
||||||
| **config_tls_certificate** | etc/server.crt | Certificate file path for API. Mandatory if proxy_address_tls is set, else optional |
|
| **config_tls_certificate** | etc/server.crt | Certificate file path for API. Mandatory if proxy_address_tls is set, else optional |
|
||||||
| **config_tls_key_file** | etc/key.pem | Private Key file path. Mandatory if proxy_address_tls is set, else optional |
|
| **proxy_tls_grade** | (high, medium, unsafe) | Grade of TLS ciphers, for easy configuration. High matches Qualys SSL Labs A+ (defaults to medium) |
|
||||||
| **proxy_address_http** | 0.0.0.0:6193 | Aralez HTTP bind address |
|
| **config_tls_key_file** | etc/key.pem | Private Key file path. Mandatory if proxy_address_tls is set, else optional |
|
||||||
| **proxy_address_tls** | 0.0.0.0:6194 | Aralez HTTPS bind address (Optional) |
|
| **proxy_address_http** | 0.0.0.0:6193 | Aralez HTTP bind address |
|
||||||
| **proxy_certificates** | etc/certs/ | The directory containing certificate and key files. In a format {NAME}.crt, {NAME}.key. |
|
| **proxy_address_tls** | 0.0.0.0:6194 | Aralez HTTPS bind address (Optional) |
|
||||||
| **upstreams_conf** | etc/upstreams.yaml | The location of upstreams file |
|
| **proxy_certificates** | etc/certs/ | The directory containing certificate and key files. In a format {NAME}.crt, {NAME}.key. |
|
||||||
| **log_level** | info | Log level , possible values : info, warn, error, debug, trace, off |
|
| **upstreams_conf** | etc/upstreams.yaml | The location of upstreams file |
|
||||||
| **hc_method** | HEAD | Healthcheck method (HEAD, GET, POST are supported) UPPERCASE |
|
| **log_level** | info | Log level , possible values : info, warn, error, debug, trace, off |
|
||||||
| **hc_interval** | 2 | Interval for health checks in seconds |
|
| **hc_method** | HEAD | Healthcheck method (HEAD, GET, POST are supported) UPPERCASE |
|
||||||
| **master_key** | 5aeff7f9-7b94-447c-af60-e8c488544a3e | Master key for working with API server and JWT Secret generation |
|
| **hc_interval** | 2 | Interval for health checks in seconds |
|
||||||
| **file_server_folder** | /some/local/folder | Optional, local folder to serve |
|
| **master_key** | 5aeff7f9-7b94-447c-af60-e8c488544a3e | Master key for working with API server and JWT Secret generation |
|
||||||
| **file_server_address** | 127.0.0.1:3002 | Optional, Local address for file server. Can set as upstream for public access |
|
| **file_server_folder** | /some/local/folder | Optional, local folder to serve |
|
||||||
| **config_api_enabled** | true | Boolean to enable/disable remote config push capability |
|
| **file_server_address** | 127.0.0.1:3002 | Optional, Local address for file server. Can set as upstream for public access |
|
||||||
|
| **config_api_enabled** | true | Boolean to enable/disable remote config push capability |
|
||||||
|
|
||||||
### 🌐 `upstreams.yaml`
|
### 🌐 `upstreams.yaml`
|
||||||
|
|
||||||
@@ -177,6 +180,7 @@ authorization:
|
|||||||
myhost.mydomain.com:
|
myhost.mydomain.com:
|
||||||
paths:
|
paths:
|
||||||
"/":
|
"/":
|
||||||
|
rate_limit: 20
|
||||||
to_https: false
|
to_https: false
|
||||||
headers:
|
headers:
|
||||||
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
||||||
@@ -201,6 +205,7 @@ myhost.mydomain.com:
|
|||||||
- Requests limits are calculated per requester ip plus requested virtualhost.
|
- Requests limits are calculated per requester ip plus requested virtualhost.
|
||||||
- If the requester exceeds the limit it will receive `429 Too Many Requests` error.
|
- If the requester exceeds the limit it will receive `429 Too Many Requests` error.
|
||||||
- Optional. Rate limiter will be disabled if the parameter is entirely removed from config.
|
- Optional. Rate limiter will be disabled if the parameter is entirely removed from config.
|
||||||
|
- Requests to `myhost.mydomain.com/` will be limited to 20 requests per second.
|
||||||
- Requests to `myhost.mydomain.com/` will be proxied to `127.0.0.1` and `127.0.0.2`.
|
- Requests to `myhost.mydomain.com/` will be proxied to `127.0.0.1` and `127.0.0.2`.
|
||||||
- Plain HTTP to `myhost.mydomain.com/foo` will get 301 redirect to configured TLS port of Aralez.
|
- Plain HTTP to `myhost.mydomain.com/foo` will get 301 redirect to configured TLS port of Aralez.
|
||||||
- Requests to `myhost.mydomain.com/foo` will be proxied to `127.0.0.4` and `127.0.0.5`.
|
- Requests to `myhost.mydomain.com/foo` will be proxied to `127.0.0.4` and `127.0.0.5`.
|
||||||
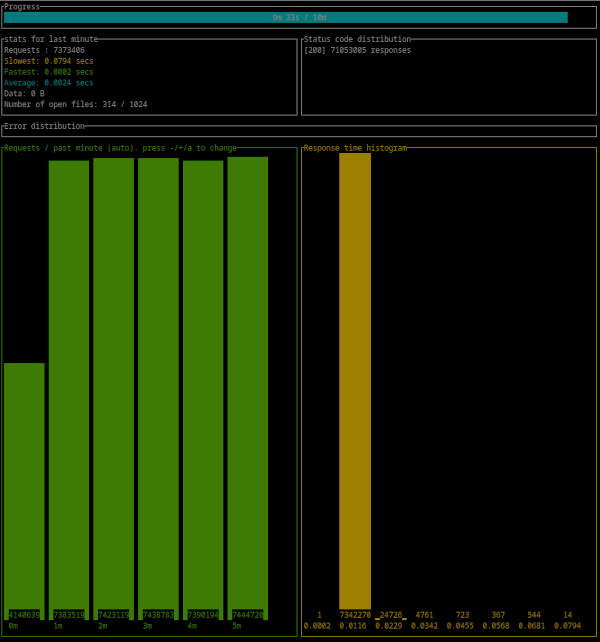
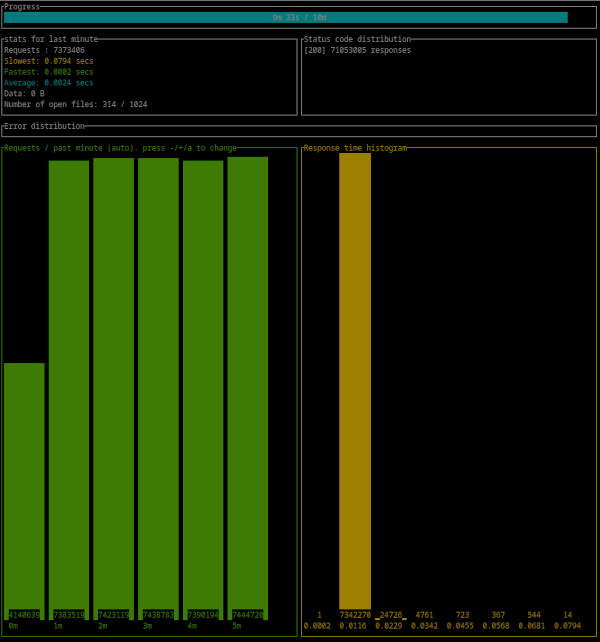
@@ -471,4 +476,21 @@ Error distribution:
|
|||||||
[228] aborted due to deadline
|
[228] aborted due to deadline
|
||||||
```
|
```
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
|
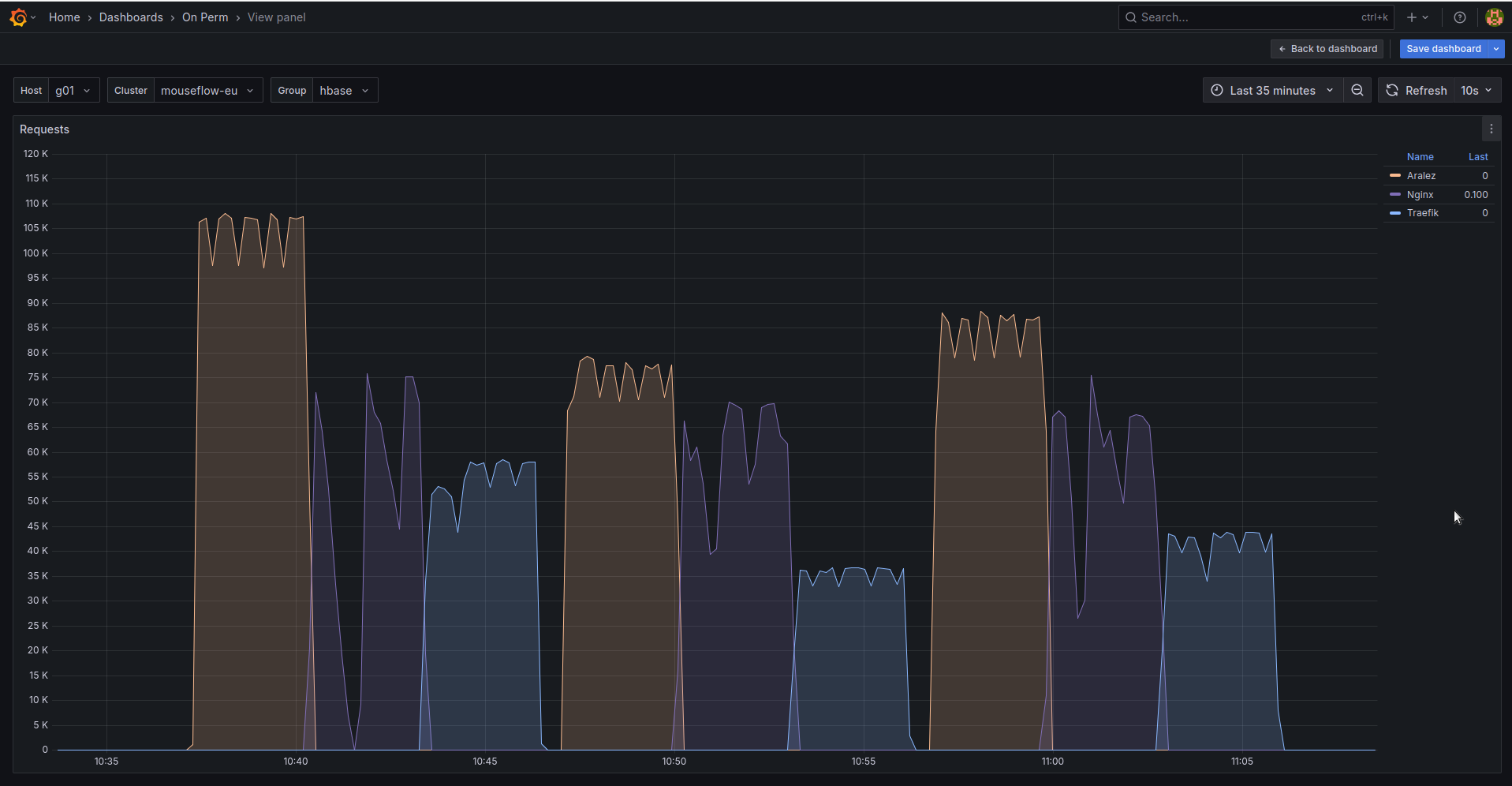
## 🚀 Aralez, Nginx, Traefik performance benchmark
|
||||||
|
|
||||||
|
This benchmark is done on 4 servers. With CPU Intel(R) Xeon(R) E-2174G CPU @ 3.80GHz, 64 GB RAM.
|
||||||
|
|
||||||
|
1. Sever runs Aralez, Traefik, Nginx on different ports. Tuned as much as I could .
|
||||||
|
2. 3x Upstreams servers, running Nginx. Replying with dummy json hardcoded in config file for max performance.
|
||||||
|
|
||||||
|
All servers are connected to the same switch with 1GB port in datacenter , not a home lab. The results:
|
||||||
|
|
||||||
|
|
||||||
|
The results show requests per second performed by Load balancer. You can see 3 batches with 800 concurrent users.
|
||||||
|
|
||||||
|
1. Requests via http1.1 to plain text endpoint.
|
||||||
|
2. Requests to via http2 to SSL endpoint.
|
||||||
|
3. Mixed workload with plain http1.1 and htt2 SSL.
|
||||||
|
|
||||||
|
|||||||
BIN
assets/bench.png
Normal file
BIN
assets/bench.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 160 KiB |
@@ -1,7 +1,7 @@
|
|||||||
# Main configuration file , applied on startup
|
# Main configuration file, applied on startup
|
||||||
threads: 12 # Nubber of daemon threads default setting
|
threads: 12 # Number of daemon threads default setting
|
||||||
#user: aralez # Username for running aralez after dropping root privileges, requires program to start as root
|
#user: pastor # Username for running aralez after dropping root privileges, requires program to start as root
|
||||||
#group: aralez # Group for running aralez after dropping root privileges, requires program to start as root
|
#group: pastor # Group for running aralez after dropping root privileges, requires program to start as root
|
||||||
daemon: false # Run in background
|
daemon: false # Run in background
|
||||||
upstream_keepalive_pool_size: 500 # Pool size for upstream keepalive connections
|
upstream_keepalive_pool_size: 500 # Pool size for upstream keepalive connections
|
||||||
pid_file: /tmp/aralez.pid # Path to PID file
|
pid_file: /tmp/aralez.pid # Path to PID file
|
||||||
@@ -10,14 +10,15 @@ upgrade_sock: /tmp/aralez.sock # Path to socket file
|
|||||||
config_api_enabled: true # Boolean to enable/disable remote config push capability.
|
config_api_enabled: true # Boolean to enable/disable remote config push capability.
|
||||||
config_address: 0.0.0.0:3000 # HTTP API address for pushing upstreams.yaml from remote location
|
config_address: 0.0.0.0:3000 # HTTP API address for pushing upstreams.yaml from remote location
|
||||||
config_tls_address: 0.0.0.0:3001 # HTTP TLS API address for pushing upstreams.yaml from remote location
|
config_tls_address: 0.0.0.0:3001 # HTTP TLS API address for pushing upstreams.yaml from remote location
|
||||||
config_tls_certificate: etc/server.crt # Mandatory if config_tls_address is set
|
config_tls_certificate: /etc/server.crt # Mandatory if config_tls_address is set
|
||||||
config_tls_key_file: etc/key.pem # Mandatory if config_tls_address is set
|
config_tls_key_file: /etc/key.pem # Mandatory if config_tls_address is set
|
||||||
proxy_address_http: 0.0.0.0:6193 # Proxy HTTP bind address
|
proxy_address_http: 0.0.0.0:6193 # Proxy HTTP bind address
|
||||||
proxy_address_tls: 0.0.0.0:6194 # Optional, Proxy TLS bind address
|
proxy_address_tls: 0.0.0.0:6194 # Optional, Proxy TLS bind address
|
||||||
proxy_certificates: etc/certificates # Mandatory if proxy_address_tls set, should contain certificate and key files strictly in a format {NAME}.crt, {NAME}.key.
|
proxy_certificates: /etc/certs # Mandatory if proxy_address_tls set, should contain a certificate and key files strictly in a format {NAME}.crt, {NAME}.key.
|
||||||
upstreams_conf: etc/upstreams.yaml # the location of upstreams file
|
proxy_tls_grade: a+ # Grade of TLS suite for proxy (a+, a, b, c, unsafe), matching grades of Qualys SSL Labs
|
||||||
#file_server_folder: /some/path # Optional, local folder to serve
|
upstreams_conf: /etc/upstreams.yaml # the location of upstreams file
|
||||||
#file_server_address: 127.0.0.1:3002 # Optional, Local address for file server. Can set as upstream for public access.
|
file_server_folder: /opt/storage # Optional, local folder to serve
|
||||||
|
file_server_address: 127.0.0.1:3002 # Optional, Local address for file server. Can set as upstream for public access.
|
||||||
log_level: info # info, warn, error, debug, trace, off
|
log_level: info # info, warn, error, debug, trace, off
|
||||||
hc_method: HEAD # Healthcheck method (HEAD, GET, POST are supported) UPPERCASE
|
hc_method: HEAD # Healthcheck method (HEAD, GET, POST are supported) UPPERCASE
|
||||||
hc_interval: 2 #Interval for health checks in seconds
|
hc_interval: 2 #Interval for health checks in seconds
|
||||||
|
|||||||
@@ -1,5 +1,5 @@
|
|||||||
# The file under watch and hot reload, changes are applied immediately, no need to restart or reload.
|
# The file under watch and hot reload, changes are applied immediately, no need to restart or reload.
|
||||||
provider: "file" # consul
|
provider: "file" # consul, kubernetes
|
||||||
sticky_sessions: false
|
sticky_sessions: false
|
||||||
to_ssl: false
|
to_ssl: false
|
||||||
#rate_limit: 100
|
#rate_limit: 100
|
||||||
@@ -17,20 +17,32 @@ authorization:
|
|||||||
# creds: "5ecbf799-1343-4e94-a9b5-e278af5cd313-56b45249-1839-4008-a450-a60dc76d2bae"
|
# creds: "5ecbf799-1343-4e94-a9b5-e278af5cd313-56b45249-1839-4008-a450-a60dc76d2bae"
|
||||||
consul: # If the provider is consul. Otherwise, ignored.
|
consul: # If the provider is consul. Otherwise, ignored.
|
||||||
servers:
|
servers:
|
||||||
- "http://master1:8500"
|
- "http://consul1:8500"
|
||||||
- "http://192.168.22.1:8500"
|
- "http://consul2:8500"
|
||||||
- "http://master1.foo.local:8500"
|
- "http://consul3:8500"
|
||||||
services: # proxy: The hostname to access the proxy server, real : The real service name in Consul database.
|
services: # proxy: The hostname to access the proxy server, real : The real service name in Consul database.
|
||||||
- proxy: "proxy-frontend-dev-frontend-srv"
|
- proxy: "proxy-frontend-dev-frontend-srv"
|
||||||
real: "frontend-dev-frontend-srv"
|
real: "frontend-dev-frontend-srv"
|
||||||
token: "8e2db809-845b-45e1-8b47-2c8356a09da0-a4370955-18c2-4d6e-a8f8-ffcc0b47be81" # Consul server access token, If Consul auth is enabled
|
token: "8e2db809-845b-45e1-8b47-2c8356a09da0-a4370955-18c2-4d6e-a8f8-ffcc0b47be81" # Consul server access token, If Consul auth is enabled
|
||||||
|
kubernetes:
|
||||||
|
servers:
|
||||||
|
- "172.16.0.11:5443" # KUBERNETES_SERVICE_HOST : KUBERNETES_SERVICE_PORT_HTTPS
|
||||||
|
services:
|
||||||
|
- proxy: "vt-api-service-v2"
|
||||||
|
real: "vt-api-service-v2"
|
||||||
|
- proxy: "vt-search-service"
|
||||||
|
real: "vt-search-service"
|
||||||
|
- proxy: "vt-websocket-service"
|
||||||
|
real: "vt-websocket-service"
|
||||||
|
tokenpath: "/tmp/token.txt" # /var/run/secrets/kubernetes.io/serviceaccount/token
|
||||||
upstreams:
|
upstreams:
|
||||||
myip.mydomain.com:
|
myip.mydomain.com:
|
||||||
paths:
|
paths:
|
||||||
|
rate_limit: 10 # Per path rate limit have higher priority than global rate limit. If not set, the global rate limit will be used
|
||||||
"/":
|
"/":
|
||||||
to_https: false
|
to_https: false
|
||||||
headers:
|
headers:
|
||||||
- "X-Proxy-From:Gazan"
|
- "X-Proxy-From:Aralez"
|
||||||
servers: # List of upstreams HOST:PORT
|
servers: # List of upstreams HOST:PORT
|
||||||
- "127.0.0.1:8000"
|
- "127.0.0.1:8000"
|
||||||
- "127.0.0.2:8000"
|
- "127.0.0.2:8000"
|
||||||
@@ -40,7 +52,7 @@ upstreams:
|
|||||||
to_https: true
|
to_https: true
|
||||||
headers:
|
headers:
|
||||||
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
- "X-Some-Thing:Yaaaaaaaaaaaaaaa"
|
||||||
- "X-Proxy-From:Gazan"
|
- "X-Proxy-From:Aralez"
|
||||||
servers:
|
servers:
|
||||||
- "127.0.0.1:8000"
|
- "127.0.0.1:8000"
|
||||||
- "127.0.0.2:8000"
|
- "127.0.0.2:8000"
|
||||||
|
|||||||
@@ -1,9 +1,11 @@
|
|||||||
pub mod auth;
|
pub mod auth;
|
||||||
pub mod consul;
|
pub mod consul;
|
||||||
pub mod discovery;
|
pub mod discovery;
|
||||||
|
pub mod dnsclient;
|
||||||
mod filewatch;
|
mod filewatch;
|
||||||
pub mod healthcheck;
|
pub mod healthcheck;
|
||||||
pub mod jwt;
|
pub mod jwt;
|
||||||
|
pub mod kuber;
|
||||||
pub mod metrics;
|
pub mod metrics;
|
||||||
pub mod parceyaml;
|
pub mod parceyaml;
|
||||||
pub mod structs;
|
pub mod structs;
|
||||||
|
|||||||
@@ -1,6 +1,5 @@
|
|||||||
use crate::utils::parceyaml::load_configuration;
|
use crate::utils::structs::{Configuration, InnerMap, ServiceMapping, UpstreamsDashMap};
|
||||||
use crate::utils::structs::{Configuration, ServiceMapping, UpstreamsDashMap};
|
use crate::utils::tools::{clone_dashmap_into, compare_dashmaps, print_upstreams};
|
||||||
use crate::utils::tools::{clone_dashmap_into, compare_dashmaps};
|
|
||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
use futures::channel::mpsc::Sender;
|
use futures::channel::mpsc::Sender;
|
||||||
use futures::SinkExt;
|
use futures::SinkExt;
|
||||||
@@ -11,6 +10,7 @@ use reqwest::header::{HeaderMap, HeaderValue};
|
|||||||
use serde::Deserialize;
|
use serde::Deserialize;
|
||||||
use std::collections::HashMap;
|
use std::collections::HashMap;
|
||||||
use std::sync::atomic::AtomicUsize;
|
use std::sync::atomic::AtomicUsize;
|
||||||
|
use std::sync::Arc;
|
||||||
use std::time::Duration;
|
use std::time::Duration;
|
||||||
|
|
||||||
#[derive(Debug, Deserialize)]
|
#[derive(Debug, Deserialize)]
|
||||||
@@ -27,59 +27,53 @@ struct TaggedAddress {
|
|||||||
port: u16,
|
port: u16,
|
||||||
}
|
}
|
||||||
|
|
||||||
pub async fn start(fp: String, mut toreturn: Sender<Configuration>) {
|
pub async fn start(mut toreturn: Sender<Configuration>, config: Arc<Configuration>) {
|
||||||
let config = load_configuration(fp.as_str(), "filepath");
|
|
||||||
let headers = DashMap::new();
|
let headers = DashMap::new();
|
||||||
match config {
|
info!("Consul Discovery is enabled : {}", config.typecfg);
|
||||||
Some(config) => {
|
let consul = config.consul.clone();
|
||||||
if config.typecfg.to_string() != "consul" {
|
let prev_upstreams = UpstreamsDashMap::new();
|
||||||
info!("Not running Consul discovery, requested type is: {}", config.typecfg);
|
match consul {
|
||||||
return;
|
Some(consul) => {
|
||||||
}
|
let servers = consul.servers.unwrap();
|
||||||
|
info!("Consul Servers => {:?}", servers);
|
||||||
|
let end = servers.len() - 1;
|
||||||
|
|
||||||
info!("Consul Discovery is enabled : {}", config.typecfg);
|
loop {
|
||||||
let consul = config.consul.clone();
|
let mut num = 0;
|
||||||
let prev_upstreams = UpstreamsDashMap::new();
|
if end > 0 {
|
||||||
match consul {
|
num = rand::rng().random_range(0..end);
|
||||||
Some(consul) => {
|
|
||||||
let servers = consul.servers.unwrap();
|
|
||||||
info!("Consul Servers => {:?}", servers);
|
|
||||||
let end = servers.len();
|
|
||||||
|
|
||||||
loop {
|
|
||||||
let num = rand::rng().random_range(1..end);
|
|
||||||
headers.clear();
|
|
||||||
for (k, v) in config.headers.clone() {
|
|
||||||
headers.insert(k.to_string(), v);
|
|
||||||
}
|
|
||||||
let consul_data = servers.get(num).unwrap().to_string();
|
|
||||||
let upstreams = consul_request(consul_data, consul.services.clone(), consul.token.clone());
|
|
||||||
match upstreams.await {
|
|
||||||
Some(upstreams) => {
|
|
||||||
if !compare_dashmaps(&upstreams, &prev_upstreams) {
|
|
||||||
let mut tosend: Configuration = Configuration {
|
|
||||||
upstreams: Default::default(),
|
|
||||||
headers: Default::default(),
|
|
||||||
consul: None,
|
|
||||||
typecfg: "".to_string(),
|
|
||||||
extraparams: config.extraparams.clone(),
|
|
||||||
};
|
|
||||||
|
|
||||||
clone_dashmap_into(&upstreams, &prev_upstreams);
|
|
||||||
clone_dashmap_into(&upstreams, &tosend.upstreams);
|
|
||||||
tosend.headers = headers.clone();
|
|
||||||
tosend.extraparams.authentication = config.extraparams.authentication.clone();
|
|
||||||
tosend.typecfg = config.typecfg.clone();
|
|
||||||
tosend.consul = config.consul.clone();
|
|
||||||
toreturn.send(tosend).await.unwrap();
|
|
||||||
}
|
|
||||||
}
|
|
||||||
None => {}
|
|
||||||
}
|
|
||||||
sleep(Duration::from_secs(5)).await;
|
|
||||||
}
|
|
||||||
}
|
}
|
||||||
None => {}
|
headers.clear();
|
||||||
|
for (k, v) in config.headers.clone() {
|
||||||
|
headers.insert(k.to_string(), v);
|
||||||
|
}
|
||||||
|
let consul_data = servers.get(num).unwrap().to_string();
|
||||||
|
let upstreams = consul_request(consul_data, consul.services.clone(), consul.token.clone());
|
||||||
|
match upstreams.await {
|
||||||
|
Some(upstreams) => {
|
||||||
|
if !compare_dashmaps(&upstreams, &prev_upstreams) {
|
||||||
|
let mut tosend: Configuration = Configuration {
|
||||||
|
upstreams: Default::default(),
|
||||||
|
headers: Default::default(),
|
||||||
|
consul: None,
|
||||||
|
kubernetes: None,
|
||||||
|
typecfg: "".to_string(),
|
||||||
|
extraparams: config.extraparams.clone(),
|
||||||
|
};
|
||||||
|
|
||||||
|
clone_dashmap_into(&upstreams, &prev_upstreams);
|
||||||
|
clone_dashmap_into(&upstreams, &tosend.upstreams);
|
||||||
|
tosend.headers = headers.clone();
|
||||||
|
tosend.extraparams.authentication = config.extraparams.authentication.clone();
|
||||||
|
tosend.typecfg = config.typecfg.clone();
|
||||||
|
tosend.consul = config.consul.clone();
|
||||||
|
print_upstreams(&tosend.upstreams);
|
||||||
|
toreturn.send(tosend).await.unwrap();
|
||||||
|
}
|
||||||
|
}
|
||||||
|
None => {}
|
||||||
|
}
|
||||||
|
sleep(Duration::from_secs(5)).await;
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
None => {}
|
None => {}
|
||||||
@@ -109,7 +103,7 @@ async fn consul_request(url: String, whitelist: Option<Vec<ServiceMapping>>, tok
|
|||||||
Some(upstreams)
|
Some(upstreams)
|
||||||
}
|
}
|
||||||
|
|
||||||
async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<String, (Vec<(String, u16, bool, bool, bool)>, AtomicUsize)>> {
|
async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<String, (Vec<InnerMap>, AtomicUsize)>> {
|
||||||
let client = reqwest::Client::new();
|
let client = reqwest::Client::new();
|
||||||
let mut headers = HeaderMap::new();
|
let mut headers = HeaderMap::new();
|
||||||
if let Some(token) = token {
|
if let Some(token) = token {
|
||||||
@@ -118,7 +112,7 @@ async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<Strin
|
|||||||
let to = Duration::from_secs(1);
|
let to = Duration::from_secs(1);
|
||||||
let u = client.get(url).timeout(to).send();
|
let u = client.get(url).timeout(to).send();
|
||||||
let mut values = Vec::new();
|
let mut values = Vec::new();
|
||||||
let upstreams: DashMap<String, (Vec<(String, u16, bool, bool, bool)>, AtomicUsize)> = DashMap::new();
|
let upstreams: DashMap<String, (Vec<InnerMap>, AtomicUsize)> = DashMap::new();
|
||||||
match u.await {
|
match u.await {
|
||||||
Ok(r) => {
|
Ok(r) => {
|
||||||
let jason = r.json::<Vec<Service>>().await;
|
let jason = r.json::<Vec<Service>>().await;
|
||||||
@@ -127,7 +121,14 @@ async fn get_by_http(url: String, token: Option<String>) -> Option<DashMap<Strin
|
|||||||
for service in whitelist {
|
for service in whitelist {
|
||||||
let addr = service.tagged_addresses.get("lan_ipv4").unwrap().address.clone();
|
let addr = service.tagged_addresses.get("lan_ipv4").unwrap().address.clone();
|
||||||
let prt = service.tagged_addresses.get("lan_ipv4").unwrap().port.clone();
|
let prt = service.tagged_addresses.get("lan_ipv4").unwrap().port.clone();
|
||||||
let to_add = (addr, prt, false, false, false);
|
let to_add = InnerMap {
|
||||||
|
address: addr,
|
||||||
|
port: prt,
|
||||||
|
is_ssl: false,
|
||||||
|
is_http2: false,
|
||||||
|
to_https: false,
|
||||||
|
rate_limit: None,
|
||||||
|
};
|
||||||
values.push(to_add);
|
values.push(to_add);
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,13 +1,11 @@
|
|||||||
use crate::utils::consul;
|
|
||||||
use crate::utils::filewatch;
|
use crate::utils::filewatch;
|
||||||
use crate::utils::structs::Configuration;
|
use crate::utils::structs::Configuration;
|
||||||
|
use crate::utils::{consul, kuber};
|
||||||
use crate::web::webserver;
|
use crate::web::webserver;
|
||||||
use async_trait::async_trait;
|
use async_trait::async_trait;
|
||||||
use futures::channel::mpsc::Sender;
|
use futures::channel::mpsc::Sender;
|
||||||
|
use std::sync::Arc;
|
||||||
|
|
||||||
pub struct FromFileProvider {
|
|
||||||
pub path: String,
|
|
||||||
}
|
|
||||||
pub struct APIUpstreamProvider {
|
pub struct APIUpstreamProvider {
|
||||||
pub config_api_enabled: bool,
|
pub config_api_enabled: bool,
|
||||||
pub address: String,
|
pub address: String,
|
||||||
@@ -19,15 +17,6 @@ pub struct APIUpstreamProvider {
|
|||||||
pub file_server_folder: Option<String>,
|
pub file_server_folder: Option<String>,
|
||||||
}
|
}
|
||||||
|
|
||||||
pub struct ConsulProvider {
|
|
||||||
pub path: String,
|
|
||||||
}
|
|
||||||
|
|
||||||
#[async_trait]
|
|
||||||
pub trait Discovery {
|
|
||||||
async fn start(&self, tx: Sender<Configuration>);
|
|
||||||
}
|
|
||||||
|
|
||||||
#[async_trait]
|
#[async_trait]
|
||||||
impl Discovery for APIUpstreamProvider {
|
impl Discovery for APIUpstreamProvider {
|
||||||
async fn start(&self, toreturn: Sender<Configuration>) {
|
async fn start(&self, toreturn: Sender<Configuration>) {
|
||||||
@@ -35,6 +24,23 @@ impl Discovery for APIUpstreamProvider {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
|
pub struct FromFileProvider {
|
||||||
|
pub path: String,
|
||||||
|
}
|
||||||
|
|
||||||
|
pub struct ConsulProvider {
|
||||||
|
pub config: Arc<Configuration>,
|
||||||
|
}
|
||||||
|
|
||||||
|
pub struct KubernetesProvider {
|
||||||
|
pub config: Arc<Configuration>,
|
||||||
|
}
|
||||||
|
|
||||||
|
#[async_trait]
|
||||||
|
pub trait Discovery {
|
||||||
|
async fn start(&self, tx: Sender<Configuration>);
|
||||||
|
}
|
||||||
|
|
||||||
#[async_trait]
|
#[async_trait]
|
||||||
impl Discovery for FromFileProvider {
|
impl Discovery for FromFileProvider {
|
||||||
async fn start(&self, tx: Sender<Configuration>) {
|
async fn start(&self, tx: Sender<Configuration>) {
|
||||||
@@ -45,6 +51,13 @@ impl Discovery for FromFileProvider {
|
|||||||
#[async_trait]
|
#[async_trait]
|
||||||
impl Discovery for ConsulProvider {
|
impl Discovery for ConsulProvider {
|
||||||
async fn start(&self, tx: Sender<Configuration>) {
|
async fn start(&self, tx: Sender<Configuration>) {
|
||||||
tokio::spawn(consul::start(self.path.clone(), tx.clone()));
|
tokio::spawn(consul::start(tx.clone(), self.config.clone()));
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
#[async_trait]
|
||||||
|
impl Discovery for KubernetesProvider {
|
||||||
|
async fn start(&self, tx: Sender<Configuration>) {
|
||||||
|
tokio::spawn(kuber::start(tx.clone(), self.config.clone()));
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|||||||
158
src/utils/dnsclient.rs
Normal file
158
src/utils/dnsclient.rs
Normal file
@@ -0,0 +1,158 @@
|
|||||||
|
/*
|
||||||
|
use crate::utils::structs::InnerMap;
|
||||||
|
use dashmap::DashMap;
|
||||||
|
use hickory_client::client::{Client, ClientHandle};
|
||||||
|
use hickory_client::proto::rr::{DNSClass, Name, RecordType};
|
||||||
|
use hickory_client::proto::runtime::TokioRuntimeProvider;
|
||||||
|
use hickory_client::proto::udp::UdpClientStream;
|
||||||
|
use std::net::SocketAddr;
|
||||||
|
use std::str::FromStr;
|
||||||
|
use std::sync::atomic::AtomicUsize;
|
||||||
|
use std::time::Duration;
|
||||||
|
use tokio::sync::Mutex;
|
||||||
|
|
||||||
|
type DnsError = Box<dyn std::error::Error + Send + Sync + 'static>;
|
||||||
|
|
||||||
|
pub struct DnsClientPool {
|
||||||
|
clients: Vec<Mutex<DnsClient>>,
|
||||||
|
}
|
||||||
|
|
||||||
|
struct DnsClient {
|
||||||
|
client: Client,
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn start2(mut toreturn: Sender<Configuration>, config: Arc<Configuration>) {
|
||||||
|
let k8s = config.kubernetes.clone();
|
||||||
|
match k8s {
|
||||||
|
Some(k8s) => {
|
||||||
|
let dnserver = k8s.servers.unwrap_or(vec!["127.0.0.1:53".to_string()]);
|
||||||
|
let headers = DashMap::new();
|
||||||
|
let end = dnserver.len() - 1;
|
||||||
|
let mut num = 0;
|
||||||
|
if end > 0 {
|
||||||
|
num = rand::rng().random_range(0..end);
|
||||||
|
}
|
||||||
|
let srv = dnserver.get(num).unwrap().to_string();
|
||||||
|
let pool = DnsClientPool::new(5, srv.clone()).await;
|
||||||
|
let u = UpstreamsDashMap::new();
|
||||||
|
if let Some(whitelist) = k8s.services {
|
||||||
|
loop {
|
||||||
|
let upstreams = UpstreamsDashMap::new();
|
||||||
|
for service in whitelist.iter() {
|
||||||
|
let ret = pool.query_srv(service.real.as_str(), srv.clone()).await;
|
||||||
|
match ret {
|
||||||
|
Ok(r) => {
|
||||||
|
upstreams.insert(service.proxy.clone(), r);
|
||||||
|
}
|
||||||
|
Err(e) => eprintln!("DNS query failed for {:?}: {:?}", service, e),
|
||||||
|
}
|
||||||
|
}
|
||||||
|
if !compare_dashmaps(&u, &upstreams) {
|
||||||
|
headers.clear();
|
||||||
|
for (k, v) in config.headers.clone() {
|
||||||
|
headers.insert(k.to_string(), v);
|
||||||
|
}
|
||||||
|
|
||||||
|
let mut tosend: Configuration = Configuration {
|
||||||
|
upstreams: Default::default(),
|
||||||
|
headers: Default::default(),
|
||||||
|
consul: None,
|
||||||
|
kubernetes: None,
|
||||||
|
typecfg: "".to_string(),
|
||||||
|
extraparams: config.extraparams.clone(),
|
||||||
|
};
|
||||||
|
|
||||||
|
clone_dashmap_into(&upstreams, &u);
|
||||||
|
clone_dashmap_into(&upstreams, &tosend.upstreams);
|
||||||
|
tosend.headers = headers.clone();
|
||||||
|
tosend.extraparams.authentication = config.extraparams.authentication.clone();
|
||||||
|
tosend.typecfg = config.typecfg.clone();
|
||||||
|
tosend.consul = config.consul.clone();
|
||||||
|
print_upstreams(&tosend.upstreams);
|
||||||
|
toreturn.send(tosend).await.unwrap();
|
||||||
|
}
|
||||||
|
|
||||||
|
tokio::time::sleep(Duration::from_secs(1)).await;
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
None => {}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
impl DnsClient {
|
||||||
|
pub async fn new(server: String) -> Result<Self, DnsError> {
|
||||||
|
let server_details = server;
|
||||||
|
let server: SocketAddr = server_details.parse().expect("Unable to parse socket address");
|
||||||
|
let conn = UdpClientStream::builder(server, TokioRuntimeProvider::default()).build();
|
||||||
|
let (client, bg) = Client::connect(conn).await.unwrap();
|
||||||
|
tokio::spawn(bg);
|
||||||
|
Ok(Self { client })
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn query_srv(&mut self, name: &str) -> Result<DashMap<String, (Vec<InnerMap>, AtomicUsize)>, DnsError> {
|
||||||
|
let upstreams: DashMap<String, (Vec<InnerMap>, AtomicUsize)> = DashMap::new();
|
||||||
|
let mut values = Vec::new();
|
||||||
|
match tokio::time::timeout(Duration::from_secs(5), self.client.query(Name::from_str(name)?, DNSClass::IN, RecordType::SRV)).await {
|
||||||
|
Ok(Ok(response)) => {
|
||||||
|
for answer in response.answers() {
|
||||||
|
if let hickory_client::proto::rr::RData::SRV(srv) = answer.data() {
|
||||||
|
let to_add = InnerMap {
|
||||||
|
address: srv.target().to_string(),
|
||||||
|
port: srv.port(),
|
||||||
|
is_ssl: false,
|
||||||
|
is_http2: false,
|
||||||
|
to_https: false,
|
||||||
|
rate_limit: None,
|
||||||
|
};
|
||||||
|
values.push(to_add);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
upstreams.insert("/".to_string(), (values, AtomicUsize::new(0)));
|
||||||
|
Ok(upstreams)
|
||||||
|
}
|
||||||
|
Ok(Err(e)) => Err(Box::new(e)),
|
||||||
|
Err(_) => Err("DNS query timed out".into()),
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
impl DnsClientPool {
|
||||||
|
pub async fn new(pool_size: usize, server: String) -> Self {
|
||||||
|
let mut clients = Vec::with_capacity(pool_size);
|
||||||
|
for _ in 0..pool_size {
|
||||||
|
if let Ok(client) = DnsClient::new(server.clone()).await {
|
||||||
|
clients.push(Mutex::new(client));
|
||||||
|
}
|
||||||
|
}
|
||||||
|
Self { clients }
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn query_srv(&self, name: &str, server: String) -> Result<DashMap<String, (Vec<InnerMap>, AtomicUsize)>, DnsError> {
|
||||||
|
// Try to get an available client
|
||||||
|
for client_mutex in &self.clients {
|
||||||
|
if let Ok(mut client) = client_mutex.try_lock() {
|
||||||
|
let vay = client.query_srv(name).await;
|
||||||
|
match vay {
|
||||||
|
Ok(_) => return vay,
|
||||||
|
Err(_) => {
|
||||||
|
// If query fails, drop this client and create a new one
|
||||||
|
*client = match DnsClient::new(server).await {
|
||||||
|
Ok(c) => c,
|
||||||
|
Err(e) => return Err(e),
|
||||||
|
};
|
||||||
|
// Retry with the new client
|
||||||
|
return client.query_srv(name).await;
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
// If all clients are busy, wait for the first one with a timeout
|
||||||
|
match tokio::time::timeout(Duration::from_secs(2), self.clients[0].lock()).await {
|
||||||
|
Ok(mut client) => client.query_srv(name).await,
|
||||||
|
Err(_) => Err("All DNS clients are busy and timeout reached".into()),
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
*/
|
||||||
@@ -2,7 +2,7 @@ use crate::utils::parceyaml::load_configuration;
|
|||||||
use crate::utils::structs::Configuration;
|
use crate::utils::structs::Configuration;
|
||||||
use futures::channel::mpsc::Sender;
|
use futures::channel::mpsc::Sender;
|
||||||
use futures::SinkExt;
|
use futures::SinkExt;
|
||||||
use log::{error, info, warn};
|
use log::error;
|
||||||
use notify::event::ModifyKind;
|
use notify::event::ModifyKind;
|
||||||
use notify::{Config, Event, EventKind, RecommendedWatcher, RecursiveMode, Watcher};
|
use notify::{Config, Event, EventKind, RecommendedWatcher, RecursiveMode, Watcher};
|
||||||
use pingora::prelude::sleep;
|
use pingora::prelude::sleep;
|
||||||
@@ -15,19 +15,7 @@ pub async fn start(fp: String, mut toreturn: Sender<Configuration>) {
|
|||||||
let file_path = fp.as_str();
|
let file_path = fp.as_str();
|
||||||
let parent_dir = Path::new(file_path).parent().unwrap();
|
let parent_dir = Path::new(file_path).parent().unwrap();
|
||||||
let (local_tx, mut local_rx) = tokio::sync::mpsc::channel::<notify::Result<Event>>(1);
|
let (local_tx, mut local_rx) = tokio::sync::mpsc::channel::<notify::Result<Event>>(1);
|
||||||
let snd = load_configuration(file_path, "filepath");
|
|
||||||
|
|
||||||
match snd {
|
|
||||||
Some(snd) => {
|
|
||||||
if snd.typecfg != "file" {
|
|
||||||
warn!("Disabling file watcher, requested discovery type is: {}", snd.typecfg);
|
|
||||||
return;
|
|
||||||
}
|
|
||||||
info!("Watching for changes in {:?}", parent_dir);
|
|
||||||
toreturn.send(snd).await.unwrap();
|
|
||||||
}
|
|
||||||
None => {}
|
|
||||||
}
|
|
||||||
let _watcher_handle = task::spawn_blocking({
|
let _watcher_handle = task::spawn_blocking({
|
||||||
let parent_dir = parent_dir.to_path_buf(); // Move directory path into the closure
|
let parent_dir = parent_dir.to_path_buf(); // Move directory path into the closure
|
||||||
move || {
|
move || {
|
||||||
@@ -53,7 +41,7 @@ pub async fn start(fp: String, mut toreturn: Sender<Configuration>) {
|
|||||||
if start.elapsed() > Duration::from_secs(2) {
|
if start.elapsed() > Duration::from_secs(2) {
|
||||||
start = Instant::now();
|
start = Instant::now();
|
||||||
// info!("Config File changed :=> {:?}", e);
|
// info!("Config File changed :=> {:?}", e);
|
||||||
let snd = load_configuration(file_path, "filepath");
|
let snd = load_configuration(file_path, "filepath").await;
|
||||||
match snd {
|
match snd {
|
||||||
Some(snd) => {
|
Some(snd) => {
|
||||||
toreturn.send(snd).await.unwrap();
|
toreturn.send(snd).await.unwrap();
|
||||||
|
|||||||
@@ -1,7 +1,7 @@
|
|||||||
use crate::utils::structs::{UpstreamsDashMap, UpstreamsIdMap};
|
use crate::utils::structs::{InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||||
use crate::utils::tools::*;
|
use crate::utils::tools::*;
|
||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
use log::{error, info, warn};
|
use log::{error, warn};
|
||||||
use reqwest::{Client, Version};
|
use reqwest::{Client, Version};
|
||||||
use std::sync::atomic::AtomicUsize;
|
use std::sync::atomic::AtomicUsize;
|
||||||
use std::sync::Arc;
|
use std::sync::Arc;
|
||||||
@@ -11,113 +11,96 @@ use tonic::transport::Endpoint;
|
|||||||
|
|
||||||
pub async fn hc2(upslist: Arc<UpstreamsDashMap>, fullist: Arc<UpstreamsDashMap>, idlist: Arc<UpstreamsIdMap>, params: (&str, u64)) {
|
pub async fn hc2(upslist: Arc<UpstreamsDashMap>, fullist: Arc<UpstreamsDashMap>, idlist: Arc<UpstreamsIdMap>, params: (&str, u64)) {
|
||||||
let mut period = interval(Duration::from_secs(params.1));
|
let mut period = interval(Duration::from_secs(params.1));
|
||||||
let mut first_run = 0;
|
let client = Client::builder().timeout(Duration::from_secs(params.1)).danger_accept_invalid_certs(true).build().unwrap();
|
||||||
loop {
|
loop {
|
||||||
tokio::select! {
|
tokio::select! {
|
||||||
_ = period.tick() => {
|
_ = period.tick() => {
|
||||||
let totest : UpstreamsDashMap = DashMap::new();
|
populate_upstreams(&upslist, &fullist, &idlist, params, &client).await;
|
||||||
let fclone : UpstreamsDashMap = clone_dashmap(&fullist);
|
|
||||||
for val in fclone.iter() {
|
|
||||||
let host = val.key();
|
|
||||||
let inner = DashMap::new();
|
|
||||||
let mut _scheme: (String, u16, bool, bool, bool) = ("".to_string(), 0, false, false, false);
|
|
||||||
for path_entry in val.value().iter() {
|
|
||||||
// let inner = DashMap::new();
|
|
||||||
let path = path_entry.key();
|
|
||||||
let mut innervec= Vec::new();
|
|
||||||
for k in path_entry.value().0 .iter().enumerate() {
|
|
||||||
let (ip, port, _ssl, _version, _redir) = k.1;
|
|
||||||
let mut _link = String::new();
|
|
||||||
let tls = detect_tls(ip, port).await;
|
|
||||||
let mut is_h2 = false;
|
|
||||||
|
|
||||||
// if tls.1 == Some(Version::HTTP_11) {
|
|
||||||
// println!(" V1: ==> {:?}", tls.1)
|
|
||||||
// }else if tls.1 == Some(Version::HTTP_2) {
|
|
||||||
// is_h2 = true;
|
|
||||||
// println!(" V2: ==> {:?}", tls.1)
|
|
||||||
// }
|
|
||||||
|
|
||||||
if tls.1 == Some(Version::HTTP_2) {
|
|
||||||
is_h2 = true;
|
|
||||||
// println!(" V2: ==> {} ==> {:?}", tls.0, tls.1)
|
|
||||||
}
|
|
||||||
|
|
||||||
match tls.0 {
|
|
||||||
true => _link = format!("https://{}:{}{}", ip, port, path),
|
|
||||||
false => _link = format!("http://{}:{}{}", ip, port, path),
|
|
||||||
}
|
|
||||||
// if _pref == "https://" {
|
|
||||||
// _scheme = (ip.to_string(), *port, true);
|
|
||||||
// }else {
|
|
||||||
// _scheme = (ip.to_string(), *port, false);
|
|
||||||
// }
|
|
||||||
_scheme = (ip.to_string(), *port, tls.0, is_h2, *_redir);
|
|
||||||
// let link = format!("{}{}:{}{}", _pref, ip, port, path);
|
|
||||||
let resp = http_request(_link.as_str(), params.0, "").await;
|
|
||||||
match resp.0 {
|
|
||||||
true => {
|
|
||||||
if resp.1 {
|
|
||||||
_scheme = (ip.to_string(), *port, tls.0, true, *_redir);
|
|
||||||
}
|
|
||||||
innervec.push(_scheme.clone());
|
|
||||||
}
|
|
||||||
false => {
|
|
||||||
warn!("Dead Upstream : {}", _link);
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
inner.insert(path.clone().to_owned(), (innervec, AtomicUsize::new(0)));
|
|
||||||
}
|
|
||||||
totest.insert(host.clone(), inner);
|
|
||||||
}
|
|
||||||
|
|
||||||
if first_run == 1 {
|
|
||||||
info!("Performing initial hatchecks and upstreams ssl detection");
|
|
||||||
clone_idmap_into(&totest, &idlist);
|
|
||||||
info!("Aralez is up and ready to serve requests, the upstreams list is:");
|
|
||||||
print_upstreams(&totest)
|
|
||||||
}
|
|
||||||
|
|
||||||
first_run+=1;
|
|
||||||
|
|
||||||
if ! compare_dashmaps(&totest, &upslist){
|
|
||||||
clone_dashmap_into(&totest, &upslist);
|
|
||||||
clone_idmap_into(&totest, &idlist);
|
|
||||||
}
|
|
||||||
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
#[allow(dead_code)]
|
pub async fn populate_upstreams(upslist: &Arc<UpstreamsDashMap>, fullist: &Arc<UpstreamsDashMap>, idlist: &Arc<UpstreamsIdMap>, params: (&str, u64), client: &Client) {
|
||||||
async fn http_request(url: &str, method: &str, payload: &str) -> (bool, bool) {
|
let totest = build_upstreams(fullist, params.0, client).await;
|
||||||
let client = Client::builder().danger_accept_invalid_certs(true).build().unwrap();
|
if !compare_dashmaps(&totest, upslist) {
|
||||||
let timeout = Duration::from_secs(1);
|
clone_dashmap_into(&totest, upslist);
|
||||||
|
clone_idmap_into(&totest, idlist);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn initiate_upstreams(fullist: UpstreamsDashMap) -> UpstreamsDashMap {
|
||||||
|
let client = Client::builder().timeout(Duration::from_secs(2)).danger_accept_invalid_certs(true).build().unwrap();
|
||||||
|
build_upstreams(&fullist, "HEAD", &client).await
|
||||||
|
}
|
||||||
|
|
||||||
|
async fn build_upstreams(fullist: &UpstreamsDashMap, method: &str, client: &Client) -> UpstreamsDashMap {
|
||||||
|
let totest: UpstreamsDashMap = DashMap::new();
|
||||||
|
let fclone = clone_dashmap(fullist);
|
||||||
|
for val in fclone.iter() {
|
||||||
|
let host = val.key();
|
||||||
|
let inner = DashMap::new();
|
||||||
|
|
||||||
|
for path_entry in val.value().iter() {
|
||||||
|
let path = path_entry.key();
|
||||||
|
let mut innervec = Vec::new();
|
||||||
|
|
||||||
|
for (_, upstream) in path_entry.value().0.iter().enumerate() {
|
||||||
|
let tls = detect_tls(upstream.address.as_str(), &upstream.port, &client).await;
|
||||||
|
let is_h2 = matches!(tls.1, Some(Version::HTTP_2));
|
||||||
|
|
||||||
|
let link = if tls.0 {
|
||||||
|
format!("https://{}:{}{}", upstream.address, upstream.port, path)
|
||||||
|
} else {
|
||||||
|
format!("http://{}:{}{}", upstream.address, upstream.port, path)
|
||||||
|
};
|
||||||
|
|
||||||
|
let mut scheme = InnerMap {
|
||||||
|
address: upstream.address.clone(),
|
||||||
|
port: upstream.port,
|
||||||
|
is_ssl: tls.0,
|
||||||
|
is_http2: is_h2,
|
||||||
|
to_https: upstream.to_https,
|
||||||
|
rate_limit: upstream.rate_limit,
|
||||||
|
};
|
||||||
|
|
||||||
|
let resp = http_request(&link, method, "", &client).await;
|
||||||
|
if resp.0 {
|
||||||
|
if resp.1 {
|
||||||
|
scheme.is_http2 = is_h2; // could be adjusted further
|
||||||
|
}
|
||||||
|
innervec.push(scheme);
|
||||||
|
} else {
|
||||||
|
warn!("Dead Upstream : {}", link);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
inner.insert(path.clone(), (innervec, AtomicUsize::new(0)));
|
||||||
|
}
|
||||||
|
totest.insert(host.clone(), inner);
|
||||||
|
}
|
||||||
|
totest
|
||||||
|
}
|
||||||
|
|
||||||
|
async fn http_request(url: &str, method: &str, payload: &str, client: &Client) -> (bool, bool) {
|
||||||
if !["POST", "GET", "HEAD"].contains(&method) {
|
if !["POST", "GET", "HEAD"].contains(&method) {
|
||||||
error!("Method {} not supported. Only GET|POST|HEAD are supported ", method);
|
error!("Method {} not supported. Only GET|POST|HEAD are supported ", method);
|
||||||
return (false, false);
|
return (false, false);
|
||||||
}
|
}
|
||||||
async fn send_request(client: &Client, method: &str, url: &str, payload: &str, timeout: Duration) -> Option<reqwest::Response> {
|
async fn send_request(client: &Client, method: &str, url: &str, payload: &str) -> Option<reqwest::Response> {
|
||||||
match method {
|
match method {
|
||||||
"POST" => client.post(url).body(payload.to_owned()).timeout(timeout).send().await.ok(),
|
"POST" => client.post(url).body(payload.to_owned()).send().await.ok(),
|
||||||
"GET" => client.get(url).timeout(timeout).send().await.ok(),
|
"GET" => client.get(url).send().await.ok(),
|
||||||
"HEAD" => client.head(url).timeout(timeout).send().await.ok(),
|
"HEAD" => client.head(url).send().await.ok(),
|
||||||
_ => None,
|
_ => None,
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
match send_request(&client, method, url, payload, timeout).await {
|
match send_request(&client, method, url, payload).await {
|
||||||
Some(response) => {
|
Some(response) => {
|
||||||
let status = response.status().as_u16();
|
let status = response.status().as_u16();
|
||||||
((99..499).contains(&status), false)
|
((99..499).contains(&status), false)
|
||||||
}
|
}
|
||||||
None => {
|
None => (ping_grpc(&url).await, true),
|
||||||
// let fallback_url = url.replace("https", "http");
|
|
||||||
// ping_grpc(&fallback_url).await
|
|
||||||
(ping_grpc(&url).await, true)
|
|
||||||
}
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
@@ -128,10 +111,7 @@ pub async fn ping_grpc(addr: &str) -> bool {
|
|||||||
let endpoint = endpoint.timeout(Duration::from_secs(2));
|
let endpoint = endpoint.timeout(Duration::from_secs(2));
|
||||||
|
|
||||||
match tokio::time::timeout(Duration::from_secs(3), endpoint.connect()).await {
|
match tokio::time::timeout(Duration::from_secs(3), endpoint.connect()).await {
|
||||||
Ok(Ok(_channel)) => {
|
Ok(Ok(_channel)) => true,
|
||||||
// println!("{:?} ==> {:?} ==> {}", endpoint, _channel, addr);
|
|
||||||
true
|
|
||||||
}
|
|
||||||
_ => false,
|
_ => false,
|
||||||
}
|
}
|
||||||
} else {
|
} else {
|
||||||
@@ -139,15 +119,24 @@ pub async fn ping_grpc(addr: &str) -> bool {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
async fn detect_tls(ip: &str, port: &u16) -> (bool, Option<Version>) {
|
async fn detect_tls(ip: &str, port: &u16, client: &Client) -> (bool, Option<Version>) {
|
||||||
let url = format!("https://{}:{}", ip, port);
|
let https_url = format!("https://{}:{}", ip, port);
|
||||||
// let url = format!("{}:{}", ip, port);
|
match client.get(&https_url).send().await {
|
||||||
let client = Client::builder().timeout(Duration::from_secs(2)).danger_accept_invalid_certs(true).build().unwrap();
|
Ok(response) => {
|
||||||
match client.get(&url).send().await {
|
// println!("{} => {:?} (HTTPS)", https_url, response.version());
|
||||||
Ok(response) => (true, Some(response.version())),
|
return (true, Some(response.version()));
|
||||||
Err(e) => {
|
}
|
||||||
if e.is_builder() || e.is_connect() || e.to_string().contains("tls") {
|
_ => {}
|
||||||
(false, None)
|
}
|
||||||
|
let http_url = format!("http://{}:{}", ip, port);
|
||||||
|
match client.get(&http_url).send().await {
|
||||||
|
Ok(response) => {
|
||||||
|
// println!("{} => {:?} (HTTP)", http_url, response.version());
|
||||||
|
(false, Some(response.version()))
|
||||||
|
}
|
||||||
|
Err(_) => {
|
||||||
|
if ping_grpc(&http_url).await {
|
||||||
|
(false, Some(Version::HTTP_2))
|
||||||
} else {
|
} else {
|
||||||
(false, None)
|
(false, None)
|
||||||
}
|
}
|
||||||
|
|||||||
133
src/utils/kuber.rs
Normal file
133
src/utils/kuber.rs
Normal file
@@ -0,0 +1,133 @@
|
|||||||
|
// use crate::utils::dnsclient::DnsClientPool;
|
||||||
|
use crate::utils::structs::{Configuration, InnerMap, UpstreamsDashMap};
|
||||||
|
use crate::utils::tools::{clone_dashmap_into, compare_dashmaps, print_upstreams};
|
||||||
|
use dashmap::DashMap;
|
||||||
|
use futures::channel::mpsc::Sender;
|
||||||
|
use futures::SinkExt;
|
||||||
|
use pingora::prelude::sleep;
|
||||||
|
use rand::Rng;
|
||||||
|
use reqwest::Client;
|
||||||
|
use std::env;
|
||||||
|
use std::sync::atomic::AtomicUsize;
|
||||||
|
use std::sync::Arc;
|
||||||
|
use std::time::Duration;
|
||||||
|
use tokio::fs::File;
|
||||||
|
use tokio::io::AsyncReadExt;
|
||||||
|
|
||||||
|
// static KUBERNETES_SERVICE_HOST: &str = "140.238.122.18:6443";
|
||||||
|
// static TOKEN: &str = "eyJhbGciOiJSUzI1NiIsImtpZCI6InJXMzl2VFlHTDM4V0tBbWxNQnRhbnRVcDlvcS10MjRDVHNwc2p3d1ZXeDAifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzg4MjY3OTgxLCJpYXQiOjE3NTY3MzE5ODEsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiMDM4ZWVlODAtNGViZi00MjU5LWI0OTctYmYwNDgxMmYyNWJhIiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJzdGFnaW5nIiwibm9kZSI6eyJuYW1lIjoiMTcyLjE2LjAuMTU1IiwidWlkIjoiOGY2ZTk2ZjYtNDdjNS00YjZhLTkwMmUtYmZhZTUwNzcxMWFjIn0sInBvZCI6eyJuYW1lIjoiYXJhbGV6LTY3Njg5OGY5ZDUtaHpienEiLCJ1aWQiOiI2NjAyZDFjNy00ZWM2LTRiZDEtYTc3NS00NzI5OGYyMTc0N2QifSwic2VydmljZWFjY291bnQiOnsibmFtZSI6ImFyYWxlei1zYSIsInVpZCI6IjVjYmYxZTU2LTJjY2YtNDFlMS05OGU2LTc3NmY1ZWY1NGRkOCJ9LCJ3YXJuYWZ0ZXIiOjE3NTY3MzU1ODh9LCJuYmYiOjE3NTY3MzE5ODEsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDpzdGFnaW5nOmFyYWxlei1zYSJ9.fnlQoOMEztWx6aE4JNPCMVDVc4s8ygs1tvuU_4FoNTWnTipFivzV3duHAg5sHFnLexYEbeBzWqr1betk__ATfy5RB5UaDdg0kk2AdVjYhvUfW4FcIqPNzXBUd74BOUG8vhN6bhZTQC8Fh0eCLCn9XXwVGIO94LKi9LmLbFiDAhpQDGwbXYnI8kV4nNGRE3kf0fsb6SyHs_8bOGc-t2U6OPdAFqBsk4JliaqiXhJKsoc8JCfUkcxYkT7GqIZxFYpvgisbOdZL7_iVyLU1BiSPMHb0jFa4O60aZ8EzCR7Mio0F5A8eZjSCf_f90ecUCGFuW3eCTCDd02RutXeSyPqxhQ";
|
||||||
|
|
||||||
|
#[derive(Debug, serde::Deserialize)]
|
||||||
|
struct Endpoints {
|
||||||
|
subsets: Option<Vec<Subset>>,
|
||||||
|
}
|
||||||
|
|
||||||
|
#[derive(Debug, serde::Deserialize)]
|
||||||
|
struct Subset {
|
||||||
|
addresses: Option<Vec<Address>>,
|
||||||
|
ports: Option<Vec<Port>>,
|
||||||
|
}
|
||||||
|
|
||||||
|
#[derive(Debug, serde::Deserialize)]
|
||||||
|
struct Address {
|
||||||
|
ip: String,
|
||||||
|
}
|
||||||
|
|
||||||
|
#[derive(Debug, serde::Deserialize)]
|
||||||
|
struct Port {
|
||||||
|
// name: String,
|
||||||
|
port: u16,
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn start(mut toreturn: Sender<Configuration>, config: Arc<Configuration>) {
|
||||||
|
let upstreams = UpstreamsDashMap::new();
|
||||||
|
let prev_upstreams = UpstreamsDashMap::new();
|
||||||
|
loop {
|
||||||
|
if let Some(kuber) = config.kubernetes.clone() {
|
||||||
|
let path = kuber.tokenpath.unwrap_or("/var/run/secrets/kubernetes.io/serviceaccount/token".to_string());
|
||||||
|
let token = read_token(path.as_str()).await;
|
||||||
|
let servers = kuber.servers.unwrap_or(vec![format!(
|
||||||
|
"{}:{}",
|
||||||
|
env::var("KUBERNETES_SERVICE_HOST").unwrap_or("0.0.0.0".to_string()),
|
||||||
|
env::var("KUBERNETES_SERVICE_PORT_HTTPS").unwrap_or("0".to_string())
|
||||||
|
)]);
|
||||||
|
let end = servers.len() - 1;
|
||||||
|
let mut num = 0;
|
||||||
|
if end > 0 {
|
||||||
|
num = rand::rng().random_range(0..end);
|
||||||
|
}
|
||||||
|
let server = servers.get(num).unwrap().to_string();
|
||||||
|
|
||||||
|
if let Some(svc) = kuber.services {
|
||||||
|
for i in svc {
|
||||||
|
let url = format!("https://{}/api/v1/namespaces/staging/endpoints/{}", server, i.real);
|
||||||
|
let list = get_by_http(&*url, &*token).await;
|
||||||
|
if let Some(list) = list {
|
||||||
|
upstreams.insert(i.proxy.clone(), list);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
if !compare_dashmaps(&upstreams, &prev_upstreams) {
|
||||||
|
let tosend: Configuration = Configuration {
|
||||||
|
upstreams: Default::default(),
|
||||||
|
headers: config.headers.clone(),
|
||||||
|
consul: config.consul.clone(),
|
||||||
|
kubernetes: config.kubernetes.clone(),
|
||||||
|
typecfg: config.typecfg.clone(),
|
||||||
|
extraparams: config.extraparams.clone(),
|
||||||
|
};
|
||||||
|
|
||||||
|
clone_dashmap_into(&upstreams, &prev_upstreams);
|
||||||
|
clone_dashmap_into(&upstreams, &tosend.upstreams);
|
||||||
|
print_upstreams(&tosend.upstreams);
|
||||||
|
toreturn.send(tosend).await.unwrap();
|
||||||
|
}
|
||||||
|
sleep(Duration::from_secs(5)).await;
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
pub async fn get_by_http(url: &str, token: &str) -> Option<DashMap<String, (Vec<InnerMap>, AtomicUsize)>> {
|
||||||
|
let client = Client::builder().timeout(Duration::from_secs(2)).danger_accept_invalid_certs(true).build().ok()?;
|
||||||
|
|
||||||
|
let resp = client.get(url).bearer_auth(token).send().await.ok()?;
|
||||||
|
|
||||||
|
if !resp.status().is_success() {
|
||||||
|
eprintln!("Kubernetes API returned status: {}", resp.status());
|
||||||
|
return None;
|
||||||
|
}
|
||||||
|
|
||||||
|
let endpoints: Endpoints = resp.json().await.ok()?;
|
||||||
|
let upstreams: DashMap<String, (Vec<InnerMap>, AtomicUsize)> = DashMap::new();
|
||||||
|
|
||||||
|
if let Some(subsets) = endpoints.subsets {
|
||||||
|
for subset in subsets {
|
||||||
|
if let (Some(addresses), Some(ports)) = (subset.addresses, subset.ports) {
|
||||||
|
for addr in addresses {
|
||||||
|
let mut inner_vec = Vec::new();
|
||||||
|
for port in &ports {
|
||||||
|
let to_add = InnerMap {
|
||||||
|
address: addr.ip.clone(),
|
||||||
|
port: port.port.clone(),
|
||||||
|
is_ssl: false,
|
||||||
|
is_http2: false,
|
||||||
|
to_https: false,
|
||||||
|
rate_limit: None,
|
||||||
|
};
|
||||||
|
inner_vec.push(to_add);
|
||||||
|
}
|
||||||
|
upstreams.insert("/".to_string(), (inner_vec, AtomicUsize::new(0)));
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
Some(upstreams)
|
||||||
|
}
|
||||||
|
|
||||||
|
async fn read_token(path: &str) -> String {
|
||||||
|
let mut file = File::open(path).await.unwrap();
|
||||||
|
let mut contents = String::new();
|
||||||
|
file.read_to_string(&mut contents).await.unwrap();
|
||||||
|
contents.trim().to_string()
|
||||||
|
}
|
||||||
@@ -61,27 +61,3 @@ pub fn calc_metrics(metric_types: &MetricTypes) {
|
|||||||
REQUESTS_BY_METHOD.with_label_values(&[&metric_types.method]).inc();
|
REQUESTS_BY_METHOD.with_label_values(&[&metric_types.method]).inc();
|
||||||
RESPONSE_LATENCY.observe(metric_types.latency.as_secs_f64());
|
RESPONSE_LATENCY.observe(metric_types.latency.as_secs_f64());
|
||||||
}
|
}
|
||||||
/*
|
|
||||||
pub fn calc_metrics(method: String, code: u16, latency: Duration) {
|
|
||||||
REQUEST_COUNT.inc();
|
|
||||||
let timer = REQUEST_LATENCY.start_timer();
|
|
||||||
timer.observe_duration();
|
|
||||||
RESPONSE_CODES.with_label_values(&[&code.to_string()]).inc();
|
|
||||||
REQUESTS_BY_METHOD.with_label_values(&[&method]).inc();
|
|
||||||
RESPONSE_LATENCY.observe(latency.as_secs_f64());
|
|
||||||
}
|
|
||||||
|
|
||||||
tokio::spawn(async move {
|
|
||||||
let mut interval = tokio::time::interval(std::time::Duration::from_secs(5));
|
|
||||||
loop {
|
|
||||||
interval.tick().await;
|
|
||||||
|
|
||||||
// read Pingora stats
|
|
||||||
let stats = pingora.get_stats();
|
|
||||||
|
|
||||||
// update Prometheus metrics accordingly
|
|
||||||
REQUEST_COUNT.set(stats.requests_total);
|
|
||||||
// ... etc
|
|
||||||
}
|
|
||||||
});
|
|
||||||
*/
|
|
||||||
|
|||||||
@@ -1,139 +1,157 @@
|
|||||||
|
use crate::utils::healthcheck;
|
||||||
use crate::utils::structs::*;
|
use crate::utils::structs::*;
|
||||||
|
use crate::utils::tools::{clone_dashmap, clone_dashmap_into, print_upstreams};
|
||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
use log::{error, info, warn};
|
use log::{error, info, warn};
|
||||||
use serde_yaml::Error;
|
|
||||||
use std::collections::HashMap;
|
use std::collections::HashMap;
|
||||||
use std::fs;
|
|
||||||
use std::sync::atomic::AtomicUsize;
|
use std::sync::atomic::AtomicUsize;
|
||||||
|
// use std::sync::mpsc::{channel, Receiver, Sender};
|
||||||
|
use std::{env, fs};
|
||||||
|
// use tokio::sync::oneshot::{Receiver, Sender};
|
||||||
|
|
||||||
pub fn load_configuration(d: &str, kind: &str) -> Option<Configuration> {
|
pub async fn load_configuration(d: &str, kind: &str) -> Option<Configuration> {
|
||||||
let mut toreturn: Configuration = Configuration {
|
let yaml_data = match kind {
|
||||||
upstreams: Default::default(),
|
"filepath" => match fs::read_to_string(d) {
|
||||||
headers: Default::default(),
|
Ok(data) => {
|
||||||
consul: None,
|
info!("Reading upstreams from {}", d);
|
||||||
typecfg: "".to_string(),
|
data
|
||||||
extraparams: Extraparams {
|
}
|
||||||
sticky_sessions: false,
|
Err(e) => {
|
||||||
to_https: None,
|
error!("Reading: {}: {:?}", d, e);
|
||||||
authentication: DashMap::new(),
|
warn!("Running with empty upstreams list, update it via API");
|
||||||
rate_limit: None,
|
return None;
|
||||||
|
}
|
||||||
},
|
},
|
||||||
};
|
|
||||||
toreturn.upstreams = UpstreamsDashMap::new();
|
|
||||||
toreturn.headers = Headers::new();
|
|
||||||
|
|
||||||
let mut yaml_data = d.to_string();
|
|
||||||
match kind {
|
|
||||||
"filepath" => {
|
|
||||||
let _ = match fs::read_to_string(d) {
|
|
||||||
Ok(data) => {
|
|
||||||
info!("Reading upstreams from {}", d);
|
|
||||||
yaml_data = data
|
|
||||||
}
|
|
||||||
Err(e) => {
|
|
||||||
error!("Reading: {}: {:?}", d, e.to_string());
|
|
||||||
warn!("Running with empty upstreams list, update it via API");
|
|
||||||
return None;
|
|
||||||
}
|
|
||||||
};
|
|
||||||
}
|
|
||||||
"content" => {
|
"content" => {
|
||||||
info!("Reading upstreams from API post body");
|
info!("Reading upstreams from API post body");
|
||||||
|
d.to_string()
|
||||||
}
|
}
|
||||||
_ => error!("Mismatched parameter, only filepath|content is allowed "),
|
_ => {
|
||||||
}
|
error!("Mismatched parameter, only filepath|content is allowed");
|
||||||
|
return None;
|
||||||
|
}
|
||||||
|
};
|
||||||
|
|
||||||
let p: Result<Config, Error> = serde_yaml::from_str(&yaml_data);
|
let parsed: Config = match serde_yaml::from_str(&yaml_data) {
|
||||||
match p {
|
Ok(cfg) => cfg,
|
||||||
Ok(parsed) => {
|
|
||||||
let global_headers = DashMap::new();
|
|
||||||
let mut hl = Vec::new();
|
|
||||||
if let Some(headers) = &parsed.headers {
|
|
||||||
for header in headers.iter() {
|
|
||||||
if let Some((key, val)) = header.split_once(':') {
|
|
||||||
hl.push((key.to_string(), val.to_string()));
|
|
||||||
}
|
|
||||||
}
|
|
||||||
global_headers.insert("/".to_string(), hl);
|
|
||||||
toreturn.headers.insert("GLOBAL_HEADERS".to_string(), global_headers);
|
|
||||||
toreturn.extraparams.sticky_sessions = parsed.sticky_sessions;
|
|
||||||
toreturn.extraparams.to_https = parsed.to_https;
|
|
||||||
toreturn.extraparams.rate_limit = parsed.rate_limit;
|
|
||||||
}
|
|
||||||
if let Some(auth) = &parsed.authorization {
|
|
||||||
let name = auth.get("type").unwrap().to_string();
|
|
||||||
let creds = auth.get("creds").unwrap().to_string();
|
|
||||||
let val: Vec<String> = vec![name, creds];
|
|
||||||
toreturn.extraparams.authentication.insert("authorization".to_string(), val);
|
|
||||||
} else {
|
|
||||||
toreturn.extraparams.authentication = DashMap::new();
|
|
||||||
}
|
|
||||||
match parsed.provider.as_str() {
|
|
||||||
"file" => {
|
|
||||||
toreturn.typecfg = "file".to_string();
|
|
||||||
if let Some(upstream) = parsed.upstreams {
|
|
||||||
for (hostname, host_config) in upstream {
|
|
||||||
let path_map = DashMap::new();
|
|
||||||
let header_list = DashMap::new();
|
|
||||||
for (path, path_config) in host_config.paths {
|
|
||||||
let mut server_list = Vec::new();
|
|
||||||
let mut hl = Vec::new();
|
|
||||||
if let Some(headers) = &path_config.headers {
|
|
||||||
for header in headers.iter().by_ref() {
|
|
||||||
if let Some((key, val)) = header.split_once(':') {
|
|
||||||
hl.push((key.to_string(), val.to_string()));
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
header_list.insert(path.clone(), hl);
|
|
||||||
for server in path_config.servers {
|
|
||||||
if let Some((ip, port_str)) = server.split_once(':') {
|
|
||||||
if let Ok(port) = port_str.parse::<u16>() {
|
|
||||||
// let to_https = matches!(path_config.to_https, Some(true));
|
|
||||||
let to_https = path_config.to_https.unwrap_or(false);
|
|
||||||
server_list.push((ip.to_string(), port, true, false, to_https));
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
path_map.insert(path, (server_list, AtomicUsize::new(0)));
|
|
||||||
}
|
|
||||||
toreturn.headers.insert(hostname.clone(), header_list);
|
|
||||||
toreturn.upstreams.insert(hostname, path_map);
|
|
||||||
}
|
|
||||||
}
|
|
||||||
Some(toreturn)
|
|
||||||
}
|
|
||||||
"consul" => {
|
|
||||||
toreturn.typecfg = "consul".to_string();
|
|
||||||
let consul = parsed.consul;
|
|
||||||
match consul {
|
|
||||||
Some(consul) => {
|
|
||||||
toreturn.consul = Some(consul);
|
|
||||||
Some(toreturn)
|
|
||||||
}
|
|
||||||
None => None,
|
|
||||||
}
|
|
||||||
}
|
|
||||||
"kubernetes" => None,
|
|
||||||
_ => {
|
|
||||||
warn!("Unknown provider {}", parsed.provider);
|
|
||||||
None
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
Err(e) => {
|
Err(e) => {
|
||||||
error!("Failed to parse upstreams file: {}", e);
|
error!("Failed to parse upstreams file: {}", e);
|
||||||
|
return None;
|
||||||
|
}
|
||||||
|
};
|
||||||
|
|
||||||
|
let mut toreturn = Configuration::default();
|
||||||
|
|
||||||
|
populate_headers_and_auth(&mut toreturn, &parsed).await;
|
||||||
|
toreturn.typecfg = parsed.provider.clone();
|
||||||
|
|
||||||
|
match parsed.provider.as_str() {
|
||||||
|
"file" => {
|
||||||
|
populate_file_upstreams(&mut toreturn, &parsed).await;
|
||||||
|
Some(toreturn)
|
||||||
|
}
|
||||||
|
"consul" => {
|
||||||
|
toreturn.consul = parsed.consul;
|
||||||
|
toreturn.consul.is_some().then_some(toreturn)
|
||||||
|
}
|
||||||
|
"kubernetes" => {
|
||||||
|
toreturn.kubernetes = parsed.kubernetes;
|
||||||
|
toreturn.kubernetes.is_some().then_some(toreturn)
|
||||||
|
}
|
||||||
|
_ => {
|
||||||
|
warn!("Unknown provider {}", parsed.provider);
|
||||||
None
|
None
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
|
async fn populate_headers_and_auth(config: &mut Configuration, parsed: &Config) {
|
||||||
|
if let Some(headers) = &parsed.headers {
|
||||||
|
let mut hl = Vec::new();
|
||||||
|
for header in headers {
|
||||||
|
if let Some((key, val)) = header.split_once(':') {
|
||||||
|
hl.push((key.trim().to_string(), val.trim().to_string()));
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
let global_headers = DashMap::new();
|
||||||
|
global_headers.insert("/".to_string(), hl);
|
||||||
|
config.headers.insert("GLOBAL_HEADERS".to_string(), global_headers);
|
||||||
|
}
|
||||||
|
|
||||||
|
config.extraparams.sticky_sessions = parsed.sticky_sessions;
|
||||||
|
config.extraparams.to_https = parsed.to_https;
|
||||||
|
config.extraparams.rate_limit = parsed.rate_limit;
|
||||||
|
|
||||||
|
if let Some(rate) = &parsed.rate_limit {
|
||||||
|
info!("Applied Global Rate Limit : {} request per second", rate);
|
||||||
|
}
|
||||||
|
|
||||||
|
if let Some(auth) = &parsed.authorization {
|
||||||
|
let name = auth.get("type").unwrap_or(&"".to_string()).to_string();
|
||||||
|
let creds = auth.get("creds").unwrap_or(&"".to_string()).to_string();
|
||||||
|
config.extraparams.authentication.insert("authorization".to_string(), vec![name, creds]);
|
||||||
|
} else {
|
||||||
|
config.extraparams.authentication = DashMap::new();
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
async fn populate_file_upstreams(config: &mut Configuration, parsed: &Config) {
|
||||||
|
let imtdashmap = UpstreamsDashMap::new();
|
||||||
|
if let Some(upstreams) = &parsed.upstreams {
|
||||||
|
for (hostname, host_config) in upstreams {
|
||||||
|
let path_map = DashMap::new();
|
||||||
|
let header_list = DashMap::new();
|
||||||
|
for (path, path_config) in &host_config.paths {
|
||||||
|
if let Some(rate) = &path_config.rate_limit {
|
||||||
|
info!("Applied Rate Limit for {} : {} request per second", hostname, rate);
|
||||||
|
}
|
||||||
|
|
||||||
|
let mut server_list = Vec::new();
|
||||||
|
let mut hl = Vec::new();
|
||||||
|
|
||||||
|
if let Some(headers) = &path_config.headers {
|
||||||
|
for header in headers {
|
||||||
|
if let Some((key, val)) = header.split_once(':') {
|
||||||
|
hl.push((key.trim().to_string(), val.trim().to_string()));
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
header_list.insert(path.clone(), hl);
|
||||||
|
|
||||||
|
for server in &path_config.servers {
|
||||||
|
if let Some((ip, port_str)) = server.split_once(':') {
|
||||||
|
if let Ok(port) = port_str.parse::<u16>() {
|
||||||
|
server_list.push(InnerMap {
|
||||||
|
address: ip.trim().to_string(),
|
||||||
|
port,
|
||||||
|
is_ssl: true,
|
||||||
|
is_http2: false,
|
||||||
|
to_https: path_config.to_https.unwrap_or(false),
|
||||||
|
// rate_limit: rate,
|
||||||
|
rate_limit: path_config.rate_limit,
|
||||||
|
});
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
path_map.insert(path.clone(), (server_list, AtomicUsize::new(0)));
|
||||||
|
}
|
||||||
|
config.headers.insert(hostname.clone(), header_list);
|
||||||
|
imtdashmap.insert(hostname.clone(), path_map);
|
||||||
|
}
|
||||||
|
let y = clone_dashmap(&imtdashmap);
|
||||||
|
let r = healthcheck::initiate_upstreams(y).await;
|
||||||
|
clone_dashmap_into(&r, &config.upstreams);
|
||||||
|
println!("Upstream Config:");
|
||||||
|
print_upstreams(&config.upstreams);
|
||||||
|
}
|
||||||
|
}
|
||||||
pub fn parce_main_config(path: &str) -> AppConfig {
|
pub fn parce_main_config(path: &str) -> AppConfig {
|
||||||
info!("Parsing configuration");
|
|
||||||
let data = fs::read_to_string(path).unwrap();
|
let data = fs::read_to_string(path).unwrap();
|
||||||
let reply = DashMap::new();
|
let reply = DashMap::new();
|
||||||
let cfg: HashMap<String, String> = serde_yaml::from_str(&*data).expect("Failed to parse main config file");
|
let cfg: HashMap<String, String> = serde_yaml::from_str(&*data).expect("Failed to parse main config file");
|
||||||
let mut cfo: AppConfig = serde_yaml::from_str(&*data).expect("Failed to parse main config file");
|
let mut cfo: AppConfig = serde_yaml::from_str(&*data).expect("Failed to parse main config file");
|
||||||
|
log_builder(&cfo);
|
||||||
cfo.hc_method = cfo.hc_method.to_uppercase();
|
cfo.hc_method = cfo.hc_method.to_uppercase();
|
||||||
for (k, v) in cfg {
|
for (k, v) in cfg {
|
||||||
reply.insert(k.to_string(), v.to_string());
|
reply.insert(k.to_string(), v.to_string());
|
||||||
@@ -150,5 +168,52 @@ pub fn parce_main_config(path: &str) -> AppConfig {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
};
|
};
|
||||||
|
cfo.proxy_tls_grade = parce_tls_grades(cfo.proxy_tls_grade.clone());
|
||||||
cfo
|
cfo
|
||||||
}
|
}
|
||||||
|
|
||||||
|
fn parce_tls_grades(what: Option<String>) -> Option<String> {
|
||||||
|
match what {
|
||||||
|
Some(g) => match g.to_ascii_lowercase().as_str() {
|
||||||
|
"high" => {
|
||||||
|
// info!("TLS grade set to: [ HIGH ]");
|
||||||
|
Some("high".to_string())
|
||||||
|
}
|
||||||
|
"medium" => {
|
||||||
|
// info!("TLS grade set to: [ MEDIUM ]");
|
||||||
|
Some("medium".to_string())
|
||||||
|
}
|
||||||
|
"unsafe" => {
|
||||||
|
// info!("TLS grade set to: [ UNSAFE ]");
|
||||||
|
Some("unsafe".to_string())
|
||||||
|
}
|
||||||
|
_ => {
|
||||||
|
warn!("Error parsing TLS grade, defaulting to: `medium`");
|
||||||
|
Some("medium".to_string())
|
||||||
|
}
|
||||||
|
},
|
||||||
|
None => {
|
||||||
|
warn!("TLS grade not set, defaulting to: medium");
|
||||||
|
Some("b".to_string())
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
fn log_builder(conf: &AppConfig) {
|
||||||
|
let log_level = conf.log_level.clone();
|
||||||
|
unsafe {
|
||||||
|
match log_level.as_str() {
|
||||||
|
"info" => env::set_var("RUST_LOG", "info"),
|
||||||
|
"error" => env::set_var("RUST_LOG", "error"),
|
||||||
|
"warn" => env::set_var("RUST_LOG", "warn"),
|
||||||
|
"debug" => env::set_var("RUST_LOG", "debug"),
|
||||||
|
"trace" => env::set_var("RUST_LOG", "trace"),
|
||||||
|
"off" => env::set_var("RUST_LOG", "off"),
|
||||||
|
_ => {
|
||||||
|
println!("Error reading log level, defaulting to: INFO");
|
||||||
|
env::set_var("RUST_LOG", "info")
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
env_logger::builder().init();
|
||||||
|
}
|
||||||
|
|||||||
@@ -3,67 +3,82 @@ use serde::{Deserialize, Serialize};
|
|||||||
use std::collections::HashMap;
|
use std::collections::HashMap;
|
||||||
use std::sync::atomic::AtomicUsize;
|
use std::sync::atomic::AtomicUsize;
|
||||||
|
|
||||||
pub type InnerMap = (String, u16, bool, bool, bool);
|
|
||||||
pub type UpstreamsDashMap = DashMap<String, DashMap<String, (Vec<InnerMap>, AtomicUsize)>>;
|
pub type UpstreamsDashMap = DashMap<String, DashMap<String, (Vec<InnerMap>, AtomicUsize)>>;
|
||||||
|
|
||||||
pub type UpstreamsIdMap = DashMap<String, InnerMap>;
|
pub type UpstreamsIdMap = DashMap<String, InnerMap>;
|
||||||
pub type Headers = DashMap<String, DashMap<String, Vec<(String, String)>>>;
|
pub type Headers = DashMap<String, DashMap<String, Vec<(String, String)>>>;
|
||||||
|
|
||||||
#[derive(Debug, Clone, Serialize, Deserialize)]
|
#[derive(Debug, Default, Clone, Serialize, Deserialize)]
|
||||||
pub struct ServiceMapping {
|
pub struct ServiceMapping {
|
||||||
pub proxy: String,
|
pub proxy: String,
|
||||||
pub real: String,
|
pub real: String,
|
||||||
}
|
}
|
||||||
|
|
||||||
#[derive(Clone, Debug)]
|
#[derive(Clone, Debug, Default)]
|
||||||
pub struct Extraparams {
|
pub struct Extraparams {
|
||||||
pub sticky_sessions: bool,
|
pub sticky_sessions: bool,
|
||||||
pub to_https: Option<bool>,
|
pub to_https: Option<bool>,
|
||||||
pub authentication: DashMap<String, Vec<String>>,
|
pub authentication: DashMap<String, Vec<String>>,
|
||||||
pub rate_limit: Option<isize>,
|
pub rate_limit: Option<isize>,
|
||||||
}
|
}
|
||||||
|
#[derive(Clone, Default, Debug, Serialize, Deserialize)]
|
||||||
|
pub struct Kubernetes {
|
||||||
|
pub servers: Option<Vec<String>>,
|
||||||
|
pub services: Option<Vec<ServiceMapping>>,
|
||||||
|
pub tokenpath: Option<String>,
|
||||||
|
}
|
||||||
|
|
||||||
#[derive(Clone, Debug, Serialize, Deserialize)]
|
#[derive(Clone, Default, Debug, Serialize, Deserialize)]
|
||||||
pub struct Consul {
|
pub struct Consul {
|
||||||
pub servers: Option<Vec<String>>,
|
pub servers: Option<Vec<String>>,
|
||||||
pub services: Option<Vec<ServiceMapping>>,
|
pub services: Option<Vec<ServiceMapping>>,
|
||||||
pub token: Option<String>,
|
pub token: Option<String>,
|
||||||
}
|
}
|
||||||
#[derive(Debug, Serialize, Deserialize)]
|
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||||
pub struct Config {
|
pub struct Config {
|
||||||
pub provider: String,
|
pub provider: String,
|
||||||
pub sticky_sessions: bool,
|
pub sticky_sessions: bool,
|
||||||
pub to_https: Option<bool>,
|
pub to_https: Option<bool>,
|
||||||
|
#[serde(default)]
|
||||||
pub upstreams: Option<HashMap<String, HostConfig>>,
|
pub upstreams: Option<HashMap<String, HostConfig>>,
|
||||||
|
#[serde(default)]
|
||||||
pub globals: Option<HashMap<String, Vec<String>>>,
|
pub globals: Option<HashMap<String, Vec<String>>>,
|
||||||
|
#[serde(default)]
|
||||||
pub headers: Option<Vec<String>>,
|
pub headers: Option<Vec<String>>,
|
||||||
|
#[serde(default)]
|
||||||
pub authorization: Option<HashMap<String, String>>,
|
pub authorization: Option<HashMap<String, String>>,
|
||||||
|
#[serde(default)]
|
||||||
pub consul: Option<Consul>,
|
pub consul: Option<Consul>,
|
||||||
|
#[serde(default)]
|
||||||
|
pub kubernetes: Option<Kubernetes>,
|
||||||
|
#[serde(default)]
|
||||||
pub rate_limit: Option<isize>,
|
pub rate_limit: Option<isize>,
|
||||||
}
|
}
|
||||||
|
|
||||||
#[derive(Debug, Serialize, Deserialize)]
|
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||||
pub struct HostConfig {
|
pub struct HostConfig {
|
||||||
pub paths: HashMap<String, PathConfig>,
|
pub paths: HashMap<String, PathConfig>,
|
||||||
pub rate_limit: Option<isize>,
|
pub rate_limit: Option<isize>,
|
||||||
}
|
}
|
||||||
|
|
||||||
#[derive(Debug, Serialize, Deserialize)]
|
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||||
pub struct PathConfig {
|
pub struct PathConfig {
|
||||||
pub servers: Vec<String>,
|
pub servers: Vec<String>,
|
||||||
pub to_https: Option<bool>,
|
pub to_https: Option<bool>,
|
||||||
pub headers: Option<Vec<String>>,
|
pub headers: Option<Vec<String>>,
|
||||||
pub rate_limit: Option<isize>,
|
pub rate_limit: Option<isize>,
|
||||||
}
|
}
|
||||||
#[derive(Debug)]
|
#[derive(Debug, Default)]
|
||||||
pub struct Configuration {
|
pub struct Configuration {
|
||||||
pub upstreams: UpstreamsDashMap,
|
pub upstreams: UpstreamsDashMap,
|
||||||
pub headers: Headers,
|
pub headers: Headers,
|
||||||
pub consul: Option<Consul>,
|
pub consul: Option<Consul>,
|
||||||
|
pub kubernetes: Option<Kubernetes>,
|
||||||
pub typecfg: String,
|
pub typecfg: String,
|
||||||
pub extraparams: Extraparams,
|
pub extraparams: Extraparams,
|
||||||
}
|
}
|
||||||
|
|
||||||
#[derive(Debug, Deserialize)]
|
#[derive(Debug, Default, Serialize, Deserialize)]
|
||||||
pub struct AppConfig {
|
pub struct AppConfig {
|
||||||
pub hc_interval: u16,
|
pub hc_interval: u16,
|
||||||
pub hc_method: String,
|
pub hc_method: String,
|
||||||
@@ -80,6 +95,31 @@ pub struct AppConfig {
|
|||||||
pub proxy_port_tls: Option<u16>,
|
pub proxy_port_tls: Option<u16>,
|
||||||
pub local_server: Option<(String, u16)>,
|
pub local_server: Option<(String, u16)>,
|
||||||
pub proxy_certificates: Option<String>,
|
pub proxy_certificates: Option<String>,
|
||||||
|
pub proxy_tls_grade: Option<String>,
|
||||||
pub file_server_address: Option<String>,
|
pub file_server_address: Option<String>,
|
||||||
pub file_server_folder: Option<String>,
|
pub file_server_folder: Option<String>,
|
||||||
}
|
}
|
||||||
|
|
||||||
|
#[derive(Debug, Clone, PartialEq, Eq, Hash)]
|
||||||
|
pub struct InnerMap {
|
||||||
|
pub address: String,
|
||||||
|
pub port: u16,
|
||||||
|
pub is_ssl: bool,
|
||||||
|
pub is_http2: bool,
|
||||||
|
pub to_https: bool,
|
||||||
|
pub rate_limit: Option<isize>,
|
||||||
|
}
|
||||||
|
|
||||||
|
#[allow(dead_code)]
|
||||||
|
impl InnerMap {
|
||||||
|
pub fn new() -> Self {
|
||||||
|
Self {
|
||||||
|
address: Default::default(),
|
||||||
|
port: Default::default(),
|
||||||
|
is_ssl: Default::default(),
|
||||||
|
is_http2: Default::default(),
|
||||||
|
to_https: Default::default(),
|
||||||
|
rate_limit: Default::default(),
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|||||||
@@ -1,12 +1,12 @@
|
|||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
use log::error;
|
use log::{error, info, warn};
|
||||||
use pingora::tls::ssl::{select_next_proto, AlpnError, NameType, SniError, SslAlert, SslContext, SslFiletype, SslMethod, SslRef};
|
use pingora::tls::ssl::{select_next_proto, AlpnError, NameType, SniError, SslAlert, SslContext, SslFiletype, SslMethod, SslRef, SslVersion};
|
||||||
|
use pingora_core::listeners::tls::TlsSettings;
|
||||||
use rustls_pemfile::{read_one, Item};
|
use rustls_pemfile::{read_one, Item};
|
||||||
use serde::Deserialize;
|
use serde::Deserialize;
|
||||||
use std::collections::HashSet;
|
use std::collections::HashSet;
|
||||||
use std::fs::File;
|
use std::fs::File;
|
||||||
use std::io::BufReader;
|
use std::io::BufReader;
|
||||||
// use tokio::time::Instant;
|
|
||||||
use x509_parser::extensions::GeneralName;
|
use x509_parser::extensions::GeneralName;
|
||||||
use x509_parser::nom::Err as NomErr;
|
use x509_parser::nom::Err as NomErr;
|
||||||
use x509_parser::prelude::*;
|
use x509_parser::prelude::*;
|
||||||
@@ -37,12 +37,12 @@ pub struct Certificates {
|
|||||||
}
|
}
|
||||||
|
|
||||||
impl Certificates {
|
impl Certificates {
|
||||||
pub fn new(configs: &Vec<CertificateConfig>) -> Option<Self> {
|
pub fn new(configs: &Vec<CertificateConfig>, _grade: &str) -> Option<Self> {
|
||||||
let default_cert = configs.first().expect("At least one TLS certificate required");
|
let default_cert = configs.first().expect("At least one TLS certificate required");
|
||||||
let mut cert_infos = Vec::new();
|
let mut cert_infos = Vec::new();
|
||||||
let name_map: DashMap<String, SslContext> = DashMap::new();
|
let name_map: DashMap<String, SslContext> = DashMap::new();
|
||||||
for config in configs {
|
for config in configs {
|
||||||
let cert_info = load_cert_info(&config.cert_path, &config.key_path);
|
let cert_info = load_cert_info(&config.cert_path, &config.key_path, _grade);
|
||||||
match cert_info {
|
match cert_info {
|
||||||
Some(cert) => {
|
Some(cert) => {
|
||||||
for name in &cert.common_names {
|
for name in &cert.common_names {
|
||||||
@@ -106,7 +106,7 @@ impl Certificates {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
fn load_cert_info(cert_path: &str, key_path: &str) -> Option<CertificateInfo> {
|
fn load_cert_info(cert_path: &str, key_path: &str, _grade: &str) -> Option<CertificateInfo> {
|
||||||
let mut common_names = HashSet::new();
|
let mut common_names = HashSet::new();
|
||||||
let mut alt_names = HashSet::new();
|
let mut alt_names = HashSet::new();
|
||||||
|
|
||||||
@@ -185,9 +185,72 @@ fn create_ssl_context(cert_path: &str, key_path: &str) -> Result<SslContext, Box
|
|||||||
Ok(built)
|
Ok(built)
|
||||||
}
|
}
|
||||||
|
|
||||||
|
#[derive(Debug)]
|
||||||
|
pub struct CipherSuite {
|
||||||
|
pub high: &'static str,
|
||||||
|
pub medium: &'static str,
|
||||||
|
pub legacy: &'static str,
|
||||||
|
}
|
||||||
|
const CIPHERS: CipherSuite = CipherSuite {
|
||||||
|
high: "TLS_AES_256_GCM_SHA384:TLS_CHACHA20_POLY1305_SHA256:TLS_AES_128_GCM_SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305",
|
||||||
|
// aa: "TLS_AES_256_GCM_SHA384:TLS_CHACHA20_POLY1305_SHA256:TLS_AES_128_GCM_SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256",
|
||||||
|
medium: "ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:AES128-GCM-SHA256",
|
||||||
|
// cc: "AES128-SHA:DES-CBC3-SHA",
|
||||||
|
legacy: "ALL:!ADH:!LOW:!EXP:!MD5:@STRENGTH",
|
||||||
|
};
|
||||||
|
|
||||||
|
#[derive(Debug)]
|
||||||
|
pub enum TlsGrade {
|
||||||
|
HIGH,
|
||||||
|
MEDIUM,
|
||||||
|
LEGACY,
|
||||||
|
}
|
||||||
|
|
||||||
|
impl TlsGrade {
|
||||||
|
pub fn from_str(s: &str) -> Option<Self> {
|
||||||
|
match s.to_ascii_lowercase().as_str() {
|
||||||
|
"high" => Some(TlsGrade::HIGH),
|
||||||
|
"medium" => Some(TlsGrade::MEDIUM),
|
||||||
|
"unsafe" => Some(TlsGrade::LEGACY),
|
||||||
|
_ => None,
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
pub fn prefer_h2<'a>(_ssl: &mut SslRef, alpn_in: &'a [u8]) -> Result<&'a [u8], AlpnError> {
|
pub fn prefer_h2<'a>(_ssl: &mut SslRef, alpn_in: &'a [u8]) -> Result<&'a [u8], AlpnError> {
|
||||||
match select_next_proto("\x02h2\x08http/1.1".as_bytes(), alpn_in) {
|
match select_next_proto("\x02h2\x08http/1.1".as_bytes(), alpn_in) {
|
||||||
Some(p) => Ok(p),
|
Some(p) => Ok(p),
|
||||||
_ => Err(AlpnError::NOACK),
|
_ => Err(AlpnError::NOACK),
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
|
pub fn set_tsl_grade(tls_settings: &mut TlsSettings, grade: &str) {
|
||||||
|
let config_grade = TlsGrade::from_str(grade);
|
||||||
|
match config_grade {
|
||||||
|
Some(TlsGrade::HIGH) => {
|
||||||
|
let _ = tls_settings.set_min_proto_version(Some(SslVersion::TLS1_2));
|
||||||
|
// let _ = tls_settings.set_max_proto_version(Some(SslVersion::TLS1_3));
|
||||||
|
let _ = tls_settings.set_cipher_list(CIPHERS.high);
|
||||||
|
let _ = tls_settings.set_ciphersuites(CIPHERS.high);
|
||||||
|
info!("TLS grade: {:?}, => HIGH", tls_settings.options());
|
||||||
|
}
|
||||||
|
Some(TlsGrade::MEDIUM) => {
|
||||||
|
let _ = tls_settings.set_min_proto_version(Some(SslVersion::TLS1));
|
||||||
|
let _ = tls_settings.set_cipher_list(CIPHERS.medium);
|
||||||
|
let _ = tls_settings.set_ciphersuites(CIPHERS.medium);
|
||||||
|
info!("TLS grade: {:?}, => MEDIUM", tls_settings.options());
|
||||||
|
}
|
||||||
|
Some(TlsGrade::LEGACY) => {
|
||||||
|
let _ = tls_settings.set_min_proto_version(Some(SslVersion::SSL3));
|
||||||
|
let _ = tls_settings.set_cipher_list(CIPHERS.legacy);
|
||||||
|
let _ = tls_settings.set_ciphersuites(CIPHERS.legacy);
|
||||||
|
warn!("TLS grade: {:?}, => UNSAFE", tls_settings.options());
|
||||||
|
}
|
||||||
|
None => {
|
||||||
|
// Defaults to MEDIUM
|
||||||
|
let _ = tls_settings.set_min_proto_version(Some(SslVersion::TLS1));
|
||||||
|
let _ = tls_settings.set_cipher_list(CIPHERS.medium);
|
||||||
|
let _ = tls_settings.set_ciphersuites(CIPHERS.medium);
|
||||||
|
warn!("TLS grade is not detected defaulting top MEDIUM");
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|||||||
@@ -1,4 +1,4 @@
|
|||||||
use crate::utils::structs::{UpstreamsDashMap, UpstreamsIdMap};
|
use crate::utils::structs::{InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||||
use crate::utils::tls;
|
use crate::utils::tls;
|
||||||
use crate::utils::tls::CertificateConfig;
|
use crate::utils::tls::CertificateConfig;
|
||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
@@ -21,10 +21,12 @@ pub fn print_upstreams(upstreams: &UpstreamsDashMap) {
|
|||||||
|
|
||||||
for path_entry in host_entry.value().iter() {
|
for path_entry in host_entry.value().iter() {
|
||||||
let path = path_entry.key();
|
let path = path_entry.key();
|
||||||
println!(" Path: {}", path);
|
println!(" Path: {}", path);
|
||||||
|
for f in path_entry.value().0.clone() {
|
||||||
for (ip, port, ssl, vers, to_https) in path_entry.value().0.clone() {
|
println!(
|
||||||
println!(" ===> IP: {}, Port: {}, SSL: {}, H2: {}, To HTTPS: {}", ip, port, ssl, vers, to_https);
|
" IP: {}, Port: {}, SSL: {}, H2: {}, To HTTPS: {}",
|
||||||
|
f.address, f.port, f.is_ssl, f.is_http2, f.to_https
|
||||||
|
);
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
@@ -140,13 +142,21 @@ pub fn clone_idmap_into(original: &UpstreamsDashMap, cloned: &UpstreamsIdMap) {
|
|||||||
let new_vec = vec.clone();
|
let new_vec = vec.clone();
|
||||||
for x in vec.iter() {
|
for x in vec.iter() {
|
||||||
let mut id = String::new();
|
let mut id = String::new();
|
||||||
write!(&mut id, "{}:{}:{}", x.0, x.1, x.2).unwrap();
|
write!(&mut id, "{}:{}:{}", x.address, x.port, x.is_ssl).unwrap();
|
||||||
let mut hasher = Sha256::new();
|
let mut hasher = Sha256::new();
|
||||||
hasher.update(id.clone().into_bytes());
|
hasher.update(id.clone().into_bytes());
|
||||||
let hash = hasher.finalize();
|
let hash = hasher.finalize();
|
||||||
let hex_hash = base16ct::lower::encode_string(&hash);
|
let hex_hash = base16ct::lower::encode_string(&hash);
|
||||||
let hh = hex_hash[0..50].to_string();
|
let hh = hex_hash[0..50].to_string();
|
||||||
cloned.insert(id, (hh.clone(), 0000, false, false, false));
|
let to_add = InnerMap {
|
||||||
|
address: hh.clone(),
|
||||||
|
port: 0,
|
||||||
|
is_ssl: false,
|
||||||
|
is_http2: false,
|
||||||
|
to_https: false,
|
||||||
|
rate_limit: None,
|
||||||
|
};
|
||||||
|
cloned.insert(id, to_add);
|
||||||
cloned.insert(hh, x.to_owned());
|
cloned.insert(hh, x.to_owned());
|
||||||
}
|
}
|
||||||
new_inner_map.insert(path.clone(), new_vec);
|
new_inner_map.insert(path.clone(), new_vec);
|
||||||
|
|||||||
@@ -1,4 +1,5 @@
|
|||||||
use crate::utils::discovery::{APIUpstreamProvider, ConsulProvider, Discovery, FromFileProvider};
|
use crate::utils::discovery::{APIUpstreamProvider, ConsulProvider, Discovery, FromFileProvider, KubernetesProvider};
|
||||||
|
use crate::utils::parceyaml::load_configuration;
|
||||||
use crate::utils::structs::Configuration;
|
use crate::utils::structs::Configuration;
|
||||||
use crate::utils::tools::*;
|
use crate::utils::tools::*;
|
||||||
use crate::utils::*;
|
use crate::utils::*;
|
||||||
@@ -6,8 +7,8 @@ use crate::web::proxyhttp::LB;
|
|||||||
use async_trait::async_trait;
|
use async_trait::async_trait;
|
||||||
use dashmap::DashMap;
|
use dashmap::DashMap;
|
||||||
use futures::channel::mpsc;
|
use futures::channel::mpsc;
|
||||||
use futures::StreamExt;
|
use futures::{SinkExt, StreamExt};
|
||||||
use log::info;
|
use log::{error, info};
|
||||||
use pingora_core::server::ShutdownWatch;
|
use pingora_core::server::ShutdownWatch;
|
||||||
use pingora_core::services::background::BackgroundService;
|
use pingora_core::services::background::BackgroundService;
|
||||||
use std::sync::Arc;
|
use std::sync::Arc;
|
||||||
@@ -15,23 +16,38 @@ use std::sync::Arc;
|
|||||||
#[async_trait]
|
#[async_trait]
|
||||||
impl BackgroundService for LB {
|
impl BackgroundService for LB {
|
||||||
async fn start(&self, mut shutdown: ShutdownWatch) {
|
async fn start(&self, mut shutdown: ShutdownWatch) {
|
||||||
info!("Starting background service");
|
info!("Starting background service"); // tx: Sender<Configuration>
|
||||||
let (tx, mut rx) = mpsc::channel::<Configuration>(0);
|
let (mut tx, mut rx) = mpsc::channel::<Configuration>(1);
|
||||||
|
let tx_api = tx.clone();
|
||||||
|
let config = load_configuration(self.config.upstreams_conf.clone().as_str(), "filepath")
|
||||||
|
.await
|
||||||
|
.expect("Failed to load configuration");
|
||||||
|
|
||||||
let tx_file = tx.clone();
|
match config.typecfg.as_str() {
|
||||||
let tx_consul = tx.clone();
|
"file" => {
|
||||||
|
info!("Running File discovery, requested type is: {}", config.typecfg);
|
||||||
let file_load = FromFileProvider {
|
tx.send(config).await.unwrap();
|
||||||
path: self.config.upstreams_conf.clone(),
|
let file_load = FromFileProvider {
|
||||||
};
|
path: self.config.upstreams_conf.clone(),
|
||||||
let consul_load = ConsulProvider {
|
};
|
||||||
path: self.config.upstreams_conf.clone(),
|
let _ = tokio::spawn(async move { file_load.start(tx).await });
|
||||||
};
|
}
|
||||||
|
"kubernetes" => {
|
||||||
let _ = tokio::spawn(async move { file_load.start(tx_file).await });
|
info!("Running Kubernetes discovery, requested type is: {}", config.typecfg);
|
||||||
let _ = tokio::spawn(async move { consul_load.start(tx_consul).await });
|
let cf = Arc::from(config);
|
||||||
// let _ = tokio::spawn(tls::watch_certs(self.config.proxy_certificates.clone().unwrap(), self.cert_tx.clone()));
|
let kuber_load = KubernetesProvider { config: cf.clone() };
|
||||||
// let _ = tokio::spawn(tls::watch_certs(self.config.proxy_certificates.clone().unwrap(), self.cert_tx.clone())).await;
|
let _ = tokio::spawn(async move { kuber_load.start(tx).await });
|
||||||
|
}
|
||||||
|
"consul" => {
|
||||||
|
info!("Running Consul discovery, requested type is: {}", config.typecfg);
|
||||||
|
let cf = Arc::from(config);
|
||||||
|
let consul_load = ConsulProvider { config: cf.clone() };
|
||||||
|
let _ = tokio::spawn(async move { consul_load.start(tx).await });
|
||||||
|
}
|
||||||
|
_ => {
|
||||||
|
error!("Unknown discovery type: {}", config.typecfg);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
|
||||||
let api_load = APIUpstreamProvider {
|
let api_load = APIUpstreamProvider {
|
||||||
address: self.config.config_address.clone(),
|
address: self.config.config_address.clone(),
|
||||||
@@ -43,7 +59,7 @@ impl BackgroundService for LB {
|
|||||||
file_server_address: self.config.file_server_address.clone(),
|
file_server_address: self.config.file_server_address.clone(),
|
||||||
file_server_folder: self.config.file_server_folder.clone(),
|
file_server_folder: self.config.file_server_folder.clone(),
|
||||||
};
|
};
|
||||||
let tx_api = tx.clone();
|
// let tx_api = tx.clone();
|
||||||
let _ = tokio::spawn(async move { api_load.start(tx_api).await });
|
let _ = tokio::spawn(async move { api_load.start(tx_api).await });
|
||||||
|
|
||||||
let uu = self.ump_upst.clone();
|
let uu = self.ump_upst.clone();
|
||||||
|
|||||||
@@ -45,7 +45,7 @@ impl GetHost for LB {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
// println!("BMT :===> {:?}", best_match);
|
// println!("Best Match :===> {:?}", best_match);
|
||||||
best_match
|
best_match
|
||||||
}
|
}
|
||||||
fn get_header(&self, peer: &str, path: &str) -> Option<Vec<(String, String)>> {
|
fn get_header(&self, peer: &str, path: &str) -> Option<Vec<(String, String)>> {
|
||||||
|
|||||||
@@ -1,6 +1,6 @@
|
|||||||
use crate::utils::auth::authenticate;
|
use crate::utils::auth::authenticate;
|
||||||
use crate::utils::metrics::*;
|
use crate::utils::metrics::*;
|
||||||
use crate::utils::structs::{AppConfig, Extraparams, Headers, UpstreamsDashMap, UpstreamsIdMap};
|
use crate::utils::structs::{AppConfig, Extraparams, Headers, InnerMap, UpstreamsDashMap, UpstreamsIdMap};
|
||||||
use crate::web::gethosts::GetHost;
|
use crate::web::gethosts::GetHost;
|
||||||
use arc_swap::ArcSwap;
|
use arc_swap::ArcSwap;
|
||||||
use async_trait::async_trait;
|
use async_trait::async_trait;
|
||||||
@@ -18,6 +18,8 @@ use std::sync::Arc;
|
|||||||
use std::time::Duration;
|
use std::time::Duration;
|
||||||
use tokio::time::Instant;
|
use tokio::time::Instant;
|
||||||
|
|
||||||
|
static RATE_LIMITER: Lazy<Rate> = Lazy::new(|| Rate::new(Duration::from_secs(1)));
|
||||||
|
|
||||||
#[derive(Clone)]
|
#[derive(Clone)]
|
||||||
pub struct LB {
|
pub struct LB {
|
||||||
pub ump_upst: Arc<UpstreamsDashMap>,
|
pub ump_upst: Arc<UpstreamsDashMap>,
|
||||||
@@ -34,11 +36,9 @@ pub struct Context {
|
|||||||
redirect_to: String,
|
redirect_to: String,
|
||||||
start_time: Instant,
|
start_time: Instant,
|
||||||
hostname: Option<String>,
|
hostname: Option<String>,
|
||||||
|
upstream_peer: Option<InnerMap>,
|
||||||
|
extraparams: arc_swap::Guard<Arc<Extraparams>>,
|
||||||
}
|
}
|
||||||
// Rate limiter
|
|
||||||
static RATE_LIMITER: Lazy<Rate> = Lazy::new(|| Rate::new(Duration::from_secs(1)));
|
|
||||||
// max request per second per client
|
|
||||||
// static MAX_REQ_PER_SEC: isize = 1;
|
|
||||||
|
|
||||||
#[async_trait]
|
#[async_trait]
|
||||||
impl ProxyHttp for LB {
|
impl ProxyHttp for LB {
|
||||||
@@ -50,37 +50,67 @@ impl ProxyHttp for LB {
|
|||||||
redirect_to: String::new(),
|
redirect_to: String::new(),
|
||||||
start_time: Instant::now(),
|
start_time: Instant::now(),
|
||||||
hostname: None,
|
hostname: None,
|
||||||
|
upstream_peer: None,
|
||||||
|
extraparams: self.extraparams.load(),
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
async fn request_filter(&self, session: &mut Session, _ctx: &mut Self::CTX) -> Result<bool> {
|
async fn request_filter(&self, session: &mut Session, _ctx: &mut Self::CTX) -> Result<bool> {
|
||||||
if let Some(auth) = self.extraparams.load().authentication.get("authorization") {
|
let ep = _ctx.extraparams.clone();
|
||||||
|
|
||||||
|
if let Some(auth) = ep.authentication.get("authorization") {
|
||||||
let authenticated = authenticate(&auth.value(), &session);
|
let authenticated = authenticate(&auth.value(), &session);
|
||||||
if !authenticated {
|
if !authenticated {
|
||||||
let _ = session.respond_error(401).await;
|
let _ = session.respond_error(401).await;
|
||||||
warn!("Forbidden: {:?}, {}", session.client_addr(), session.req_header().uri.path().to_string());
|
warn!("Forbidden: {:?}, {}", session.client_addr(), session.req_header().uri.path());
|
||||||
return Ok(true);
|
return Ok(true);
|
||||||
}
|
}
|
||||||
};
|
};
|
||||||
|
|
||||||
let hostname = return_header_host(&session);
|
let hostname = return_header_host(&session);
|
||||||
_ctx.hostname = hostname.clone();
|
_ctx.hostname = hostname.clone();
|
||||||
if let Some(rate) = self.extraparams.load().rate_limit {
|
|
||||||
match hostname {
|
let mut backend_id = None;
|
||||||
None => return Ok(false),
|
|
||||||
Some(host) => {
|
if ep.sticky_sessions {
|
||||||
let curr_window_requests = RATE_LIMITER.observe(&host, 1);
|
if let Some(cookies) = session.req_header().headers.get("cookie") {
|
||||||
if curr_window_requests > rate {
|
if let Ok(cookie_str) = cookies.to_str() {
|
||||||
let mut header = ResponseHeader::build(429, None).unwrap();
|
for cookie in cookie_str.split(';') {
|
||||||
header.insert_header("X-Rate-Limit-Limit", rate.to_string()).unwrap();
|
let trimmed = cookie.trim();
|
||||||
header.insert_header("X-Rate-Limit-Remaining", "0").unwrap();
|
if let Some(value) = trimmed.strip_prefix("backend_id=") {
|
||||||
header.insert_header("X-Rate-Limit-Reset", "1").unwrap();
|
backend_id = Some(value);
|
||||||
session.set_keepalive(None);
|
break;
|
||||||
session.write_response_header(Box::new(header), true).await?;
|
}
|
||||||
debug!("Rate limited: {:?}, {}", session.client_addr(), rate);
|
|
||||||
return Ok(true);
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
};
|
}
|
||||||
|
}
|
||||||
|
|
||||||
|
match hostname {
|
||||||
|
None => return Ok(false),
|
||||||
|
Some(host) => {
|
||||||
|
let optioninnermap = self.get_host(host.as_str(), host.as_str(), backend_id);
|
||||||
|
match optioninnermap {
|
||||||
|
None => return Ok(false),
|
||||||
|
Some(ref innermap) => {
|
||||||
|
if let Some(rate) = innermap.rate_limit.or(ep.rate_limit) {
|
||||||
|
// let rate_key = session.client_addr().and_then(|addr| addr.as_inet()).map(|inet| inet.ip().to_string()).unwrap_or_else(|| host.to_string());
|
||||||
|
let rate_key = session.client_addr().and_then(|addr| addr.as_inet()).map(|inet| inet.ip());
|
||||||
|
let curr_window_requests = RATE_LIMITER.observe(&rate_key, 1);
|
||||||
|
if curr_window_requests > rate {
|
||||||
|
let mut header = ResponseHeader::build(429, None).unwrap();
|
||||||
|
header.insert_header("X-Rate-Limit-Limit", rate.to_string()).unwrap();
|
||||||
|
header.insert_header("X-Rate-Limit-Remaining", "0").unwrap();
|
||||||
|
header.insert_header("X-Rate-Limit-Reset", "1").unwrap();
|
||||||
|
session.set_keepalive(None);
|
||||||
|
session.write_response_header(Box::new(header), true).await?;
|
||||||
|
debug!("Rate limited: {:?}, {}", rate_key, rate);
|
||||||
|
return Ok(true);
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
_ctx.upstream_peer = optioninnermap;
|
||||||
|
}
|
||||||
}
|
}
|
||||||
Ok(false)
|
Ok(false)
|
||||||
}
|
}
|
||||||
@@ -88,38 +118,20 @@ impl ProxyHttp for LB {
|
|||||||
// let host_name = return_header_host(&session);
|
// let host_name = return_header_host(&session);
|
||||||
match ctx.hostname.as_ref() {
|
match ctx.hostname.as_ref() {
|
||||||
Some(hostname) => {
|
Some(hostname) => {
|
||||||
let mut backend_id = None;
|
match ctx.upstream_peer.as_ref() {
|
||||||
|
// Some((address, port, ssl, is_h2, to_https)) => {
|
||||||
if self.extraparams.load().sticky_sessions {
|
Some(innermap) => {
|
||||||
if let Some(cookies) = session.req_header().headers.get("cookie") {
|
let mut peer = Box::new(HttpPeer::new((innermap.address.clone(), innermap.port.clone()), innermap.is_ssl, String::new()));
|
||||||
if let Ok(cookie_str) = cookies.to_str() {
|
|
||||||
for cookie in cookie_str.split(';') {
|
|
||||||
let trimmed = cookie.trim();
|
|
||||||
if let Some(value) = trimmed.strip_prefix("backend_id=") {
|
|
||||||
backend_id = Some(value);
|
|
||||||
break;
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
|
|
||||||
let ddr = self.get_host(hostname, hostname, backend_id);
|
|
||||||
|
|
||||||
match ddr {
|
|
||||||
Some((address, port, ssl, is_h2, to_https)) => {
|
|
||||||
let mut peer = Box::new(HttpPeer::new((address.clone(), port.clone()), ssl, String::new()));
|
|
||||||
// if session.is_http2() {
|
// if session.is_http2() {
|
||||||
if is_h2 {
|
if innermap.is_http2 {
|
||||||
peer.options.alpn = ALPN::H2;
|
peer.options.alpn = ALPN::H2;
|
||||||
}
|
}
|
||||||
if ssl {
|
if innermap.is_ssl {
|
||||||
peer.sni = hostname.clone();
|
peer.sni = hostname.clone();
|
||||||
peer.options.verify_cert = false;
|
peer.options.verify_cert = false;
|
||||||
peer.options.verify_hostname = false;
|
peer.options.verify_hostname = false;
|
||||||
}
|
}
|
||||||
|
if ctx.to_https || innermap.to_https {
|
||||||
if self.extraparams.load().to_https.unwrap_or(false) || to_https {
|
|
||||||
if let Some(stream) = session.stream() {
|
if let Some(stream) = session.stream() {
|
||||||
if stream.get_ssl().is_none() {
|
if stream.get_ssl().is_none() {
|
||||||
if let Some(addr) = session.server_addr() {
|
if let Some(addr) = session.server_addr() {
|
||||||
@@ -134,7 +146,7 @@ impl ProxyHttp for LB {
|
|||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|
||||||
ctx.backend_id = format!("{}:{}:{}", address.clone(), port.clone(), ssl);
|
ctx.backend_id = format!("{}:{}:{}", innermap.address.clone(), innermap.port.clone(), innermap.is_ssl);
|
||||||
Ok(peer)
|
Ok(peer)
|
||||||
}
|
}
|
||||||
None => {
|
None => {
|
||||||
@@ -190,10 +202,10 @@ impl ProxyHttp for LB {
|
|||||||
// }
|
// }
|
||||||
async fn response_filter(&self, session: &mut Session, _upstream_response: &mut ResponseHeader, ctx: &mut Self::CTX) -> Result<()> {
|
async fn response_filter(&self, session: &mut Session, _upstream_response: &mut ResponseHeader, ctx: &mut Self::CTX) -> Result<()> {
|
||||||
// _upstream_response.insert_header("X-Proxied-From", "Fooooooooooooooo").unwrap();
|
// _upstream_response.insert_header("X-Proxied-From", "Fooooooooooooooo").unwrap();
|
||||||
if self.extraparams.load().sticky_sessions {
|
if ctx.extraparams.sticky_sessions {
|
||||||
let backend_id = ctx.backend_id.clone();
|
let backend_id = ctx.backend_id.clone();
|
||||||
if let Some(bid) = self.ump_byid.get(&backend_id) {
|
if let Some(bid) = self.ump_byid.get(&backend_id) {
|
||||||
let _ = _upstream_response.insert_header("set-cookie", format!("backend_id={}; Path=/; Max-Age=600; HttpOnly; SameSite=Lax", bid.0));
|
let _ = _upstream_response.insert_header("set-cookie", format!("backend_id={}; Path=/; Max-Age=600; HttpOnly; SameSite=Lax", bid.address));
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
if ctx.to_https {
|
if ctx.to_https {
|
||||||
@@ -202,7 +214,6 @@ impl ProxyHttp for LB {
|
|||||||
redirect_response.insert_header("Content-Length", "0")?;
|
redirect_response.insert_header("Content-Length", "0")?;
|
||||||
session.write_response_header(Box::new(redirect_response), false).await?;
|
session.write_response_header(Box::new(redirect_response), false).await?;
|
||||||
}
|
}
|
||||||
// match return_header_host(&session) {
|
|
||||||
match ctx.hostname.as_ref() {
|
match ctx.hostname.as_ref() {
|
||||||
Some(host) => {
|
Some(host) => {
|
||||||
let path = session.req_header().uri.path();
|
let path = session.req_header().uri.path();
|
||||||
|
|||||||
@@ -13,7 +13,7 @@ use pingora_core::prelude::{background_service, Opt};
|
|||||||
use pingora_core::server::Server;
|
use pingora_core::server::Server;
|
||||||
use std::sync::mpsc::{channel, Receiver, Sender};
|
use std::sync::mpsc::{channel, Receiver, Sender};
|
||||||
use std::sync::Arc;
|
use std::sync::Arc;
|
||||||
use std::{env, thread};
|
use std::thread;
|
||||||
|
|
||||||
pub fn run() {
|
pub fn run() {
|
||||||
// default_provider().install_default().expect("Failed to install rustls crypto provider");
|
// default_provider().install_default().expect("Failed to install rustls crypto provider");
|
||||||
@@ -46,23 +46,26 @@ pub fn run() {
|
|||||||
headers: hh_config,
|
headers: hh_config,
|
||||||
extraparams: ec_config,
|
extraparams: ec_config,
|
||||||
};
|
};
|
||||||
|
/*
|
||||||
let log_level = cfg.log_level.clone();
|
let log_level = cfg.log_level.clone();
|
||||||
unsafe {
|
unsafe {
|
||||||
match log_level.as_str() {
|
match log_level.as_str() {
|
||||||
"info" => env::set_var("RUST_LOG", "info"),
|
"info" => env::set_var("RUST_LOG", "info"),
|
||||||
"error" => env::set_var("RUST_LOG", "error"),
|
"error" => env::set_var("RUST_LOG", "error"),
|
||||||
"warn" => env::set_var("RUST_LOG", "warn"),
|
"warn" => env::set_var("RUST_LOG", "warn"),
|
||||||
"debug" => env::set_var("RUST_LOG", "debug"),
|
"debug" => env::set_var("RUST_LOG", "debug"),
|
||||||
"trace" => env::set_var("RUST_LOG", "trace"),
|
"trace" => env::set_var("RUST_LOG", "trace"),
|
||||||
"off" => env::set_var("RUST_LOG", "off"),
|
"off" => env::set_var("RUST_LOG", "off"),
|
||||||
_ => {
|
_ => {
|
||||||
println!("Error reading log level, defaulting to: INFO");
|
println!("Error reading log level, defaulting to: INFO");
|
||||||
env::set_var("RUST_LOG", "info")
|
env::set_var("RUST_LOG", "info")
|
||||||
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
env_logger::builder().init();
|
||||||
env_logger::builder().init();
|
*/
|
||||||
|
let grade = cfg.proxy_tls_grade.clone().unwrap_or("medium".to_string());
|
||||||
|
info!("TLS grade set to: [ {} ]", grade);
|
||||||
|
|
||||||
let bg_srvc = background_service("bgsrvc", lb.clone());
|
let bg_srvc = background_service("bgsrvc", lb.clone());
|
||||||
let mut proxy = pingora_proxy::http_proxy_service(&server.configuration, lb.clone());
|
let mut proxy = pingora_proxy::http_proxy_service(&server.configuration, lb.clone());
|
||||||
@@ -77,25 +80,27 @@ pub fn run() {
|
|||||||
watch_folder(certs_path, tx).unwrap();
|
watch_folder(certs_path, tx).unwrap();
|
||||||
});
|
});
|
||||||
let certificate_configs = rx.recv().unwrap();
|
let certificate_configs = rx.recv().unwrap();
|
||||||
let first_set = tls::Certificates::new(&certificate_configs).unwrap_or_else(|| panic!("Unable to load initial certificate info"));
|
let first_set = tls::Certificates::new(&certificate_configs, grade.as_str()).unwrap_or_else(|| panic!("Unable to load initial certificate info"));
|
||||||
let certificates = Arc::new(ArcSwap::from_pointee(first_set));
|
let certificates = Arc::new(ArcSwap::from_pointee(first_set));
|
||||||
let certs_for_callback = certificates.clone();
|
let certs_for_callback = certificates.clone();
|
||||||
|
|
||||||
let certs_for_watcher = certificates.clone();
|
let certs_for_watcher = certificates.clone();
|
||||||
let new_certs = tls::Certificates::new(&certificate_configs);
|
let new_certs = tls::Certificates::new(&certificate_configs, grade.as_str());
|
||||||
certs_for_watcher.store(Arc::new(new_certs.unwrap()));
|
certs_for_watcher.store(Arc::new(new_certs.unwrap()));
|
||||||
|
|
||||||
let mut tls_settings =
|
let mut tls_settings =
|
||||||
TlsSettings::intermediate(&certs_for_callback.load().default_cert_path, &certs_for_callback.load().default_key_path).expect("unable to load or parse cert/key");
|
TlsSettings::intermediate(&certs_for_callback.load().default_cert_path, &certs_for_callback.load().default_key_path).expect("unable to load or parse cert/key");
|
||||||
|
|
||||||
|
tls::set_tsl_grade(&mut tls_settings, grade.as_str());
|
||||||
tls_settings.set_servername_callback(move |ssl_ref: &mut SslRef, ssl_alert: &mut SslAlert| certs_for_callback.load().server_name_callback(ssl_ref, ssl_alert));
|
tls_settings.set_servername_callback(move |ssl_ref: &mut SslRef, ssl_alert: &mut SslAlert| certs_for_callback.load().server_name_callback(ssl_ref, ssl_alert));
|
||||||
tls_settings.set_alpn_select_callback(tls::prefer_h2);
|
tls_settings.set_alpn_select_callback(tls::prefer_h2);
|
||||||
|
|
||||||
proxy.add_tls_with_settings(&bind_address_tls, None, tls_settings);
|
proxy.add_tls_with_settings(&bind_address_tls, None, tls_settings);
|
||||||
|
|
||||||
let certs_for_watcher = certificates.clone();
|
let certs_for_watcher = certificates.clone();
|
||||||
thread::spawn(move || {
|
thread::spawn(move || {
|
||||||
while let Ok(new_configs) = rx.recv() {
|
while let Ok(new_configs) = rx.recv() {
|
||||||
let new_certs = tls::Certificates::new(&new_configs);
|
let new_certs = tls::Certificates::new(&new_configs, grade.as_str());
|
||||||
match new_certs {
|
match new_certs {
|
||||||
Some(new_certs) => {
|
Some(new_certs) => {
|
||||||
certs_for_watcher.store(Arc::new(new_certs));
|
certs_for_watcher.store(Arc::new(new_certs));
|
||||||
|
|||||||
@@ -92,7 +92,7 @@ async fn conf(State(mut st): State<AppState>, Query(params): Query<HashMap<Strin
|
|||||||
|
|
||||||
if let Some(s) = params.get("key") {
|
if let Some(s) = params.get("key") {
|
||||||
if s.to_owned() == st.master_key {
|
if s.to_owned() == st.master_key {
|
||||||
if let Some(serverlist) = crate::utils::parceyaml::load_configuration(content.as_str(), "content") {
|
if let Some(serverlist) = crate::utils::parceyaml::load_configuration(content.as_str(), "content").await {
|
||||||
st.config_sender.send(serverlist).await.unwrap();
|
st.config_sender.send(serverlist).await.unwrap();
|
||||||
return Response::builder().status(StatusCode::OK).body(Body::from("Config, conf file, updated !\n")).unwrap();
|
return Response::builder().status(StatusCode::OK).body(Body::from("Config, conf file, updated !\n")).unwrap();
|
||||||
} else {
|
} else {
|
||||||
|
|||||||
Reference in New Issue
Block a user